
ZeroDayRAT is a newly discovered mobile spyware service that targets both Android and iOS devices. Unlike traditional malware that focuses only on spying or financial theft, this tool combines both into a single platform. It allows attackers to monitor victims in real time while also stealing money directly from banking and cryptocurrency apps.
Security researchers from Cyberthint found that ZeroDayRAT is being sold on Telegram as a Malware-as-a-Service (MaaS). This means even non-technical criminals can subscribe, access a web-based dashboard, and control infected devices remotely.
The infection usually starts with smishing messages — fake SMS alerts pretending to be service providers or app updates. Victims are tricked into installing a malicious Android APK or iOS payload. Once installed, the attacker gains full control through a browser-based control panel.
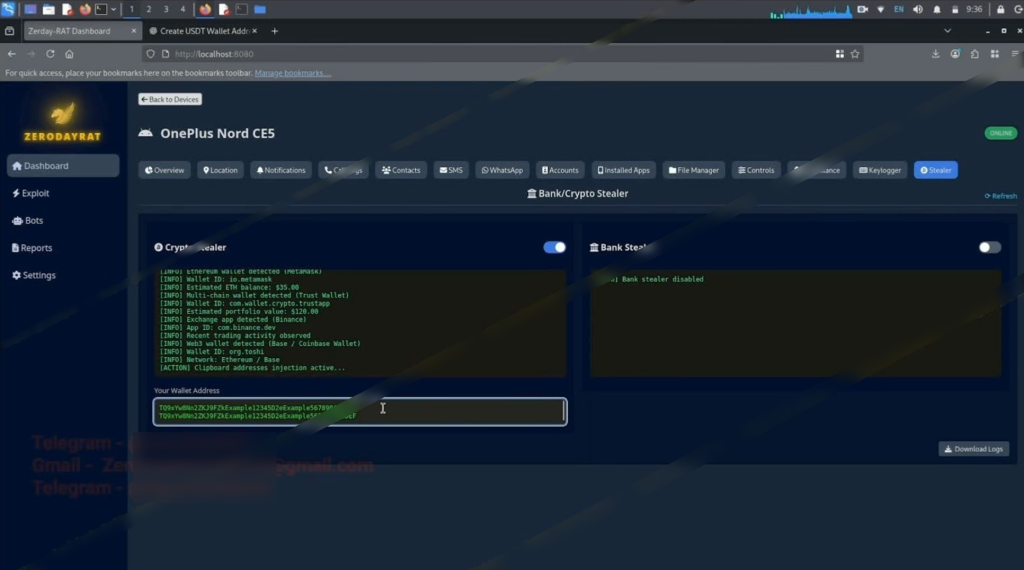
Through this dashboard, attackers can view device details, monitor messages, track GPS location, and even activate the microphone and camera. The malware also targets financial apps by using clipboard hijacking and fake login overlays to steal credentials. It can intercept OTP codes, allowing criminals to bypass two-factor authentication in real time.
ZeroDayRAT is sold in subscription tiers — $250 per day, $1000 per week, and $3500 per month — and transactions are reportedly handled through escrow services, indicating an organized criminal operation.
What Makes ZeroDayRAT Dangerous
- Real-time GPS tracking and live surveillance
- Remote camera and microphone activation
- Screen recording and keylogging
- Clipboard hijacking for cryptocurrency theft
- Fake login overlays for banking and payment apps
- OTP interception to bypass 2FA
- Easy-to-use browser control panel
- Sold as a subscription service on Telegram
Credibility Concerns
Security analysts say ZeroDayRAT appears to be a real threat, but some details raise questions. In one promotional screenshot, researchers noticed a browser tab labeled “Create USDT Wallet Address,” which looked staged or taken from demo material. This suggests that some features may be exaggerated for marketing.
Even so, the overall capability of the tool reflects a growing shift in cybercrime. Criminals can now rent advanced surveillance kits that were once limited to highly skilled actors. ZeroDayRAT joins other mobile-focused threats like Anatsa, Arsink, and NFCShare that target banking apps, crypto wallets, and everyday mobile behavior.
As mobile malware continues to evolve, users and organizations must stay cautious. Most infections still begin with simple smishing messages or fake app downloads — proving that even small actions can lead to serious compromise.
Follow Us on: Linkedin, Instagram, Facebook to get the latest security news!




