The Cybersecurity and Infrastructure Security Agency (CISA) has warned about a serious supply chain attack involving the popular Axios npm package, highlighting the potential for an axios npm hack.
Axios is a widely used JavaScript library that helps developers handle HTTP requests in both Node.js and browsers. Because it is used in so many projects, this axios npm hack can affect a large number of applications and development systems.
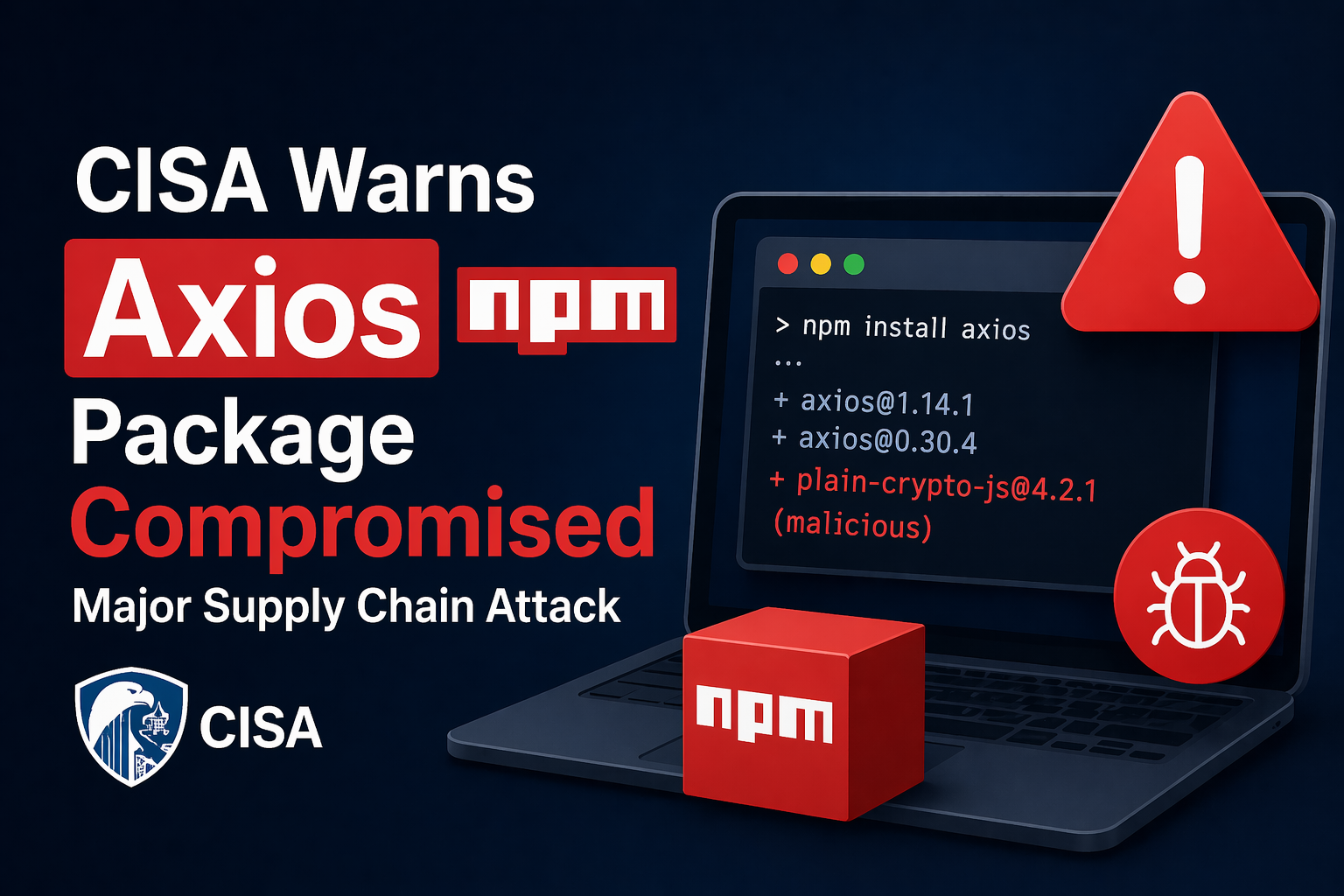
The attack took place on March 31, 2026, when hackers compromised two versions of Axios — 1.14.1 and 0.30.4. When developers installed these versions, a hidden malicious package called “plain-crypto-js” was automatically included without their knowledge, demonstrating the dangers of an axios npm hack.
This package acts as a loader. It connects to attacker-controlled servers and downloads additional malware. One of the main threats is a Remote Access Trojan (RAT), which allows attackers to gain control over infected machines.
If a developer’s system is affected, attackers can quietly steal sensitive data such as source code, environment variables, and credentials. They can also move deeper into company systems, including CI/CD pipelines, which increases the overall risk.
What You Should Do Immediately
CISA recommends that organizations review their systems for any recent Axios updates. If the affected versions were installed, quick action is important.
Teams should downgrade to safe versions like 1.14.0 or 0.30.3 and remove the malicious “plain-crypto-js” package from their projects. It is also important to rotate all sensitive credentials, including API keys, SSH keys, and access tokens.
Monitoring network activity is another key step. Any unusual outbound connections should be investigated, and security scans should be run to ensure no hidden threats remain.
How to Prevent Similar Attacks
This incident highlights how software supply chain attacks are becoming more advanced. Many of these attacks take advantage of default package manager settings that automatically install dependencies.
To reduce risk, organizations should strengthen their security practices. Enabling strong authentication for developer accounts can prevent unauthorized access. Disabling automatic script execution during installations can also block malicious behavior.
It is also a good practice to avoid using newly published packages without proper verification. Monitoring systems for unusual activity, such as unexpected processes or unknown network connections, can help detect threats early.
By taking these precautions, organizations can better protect their development environments from future attacks.




