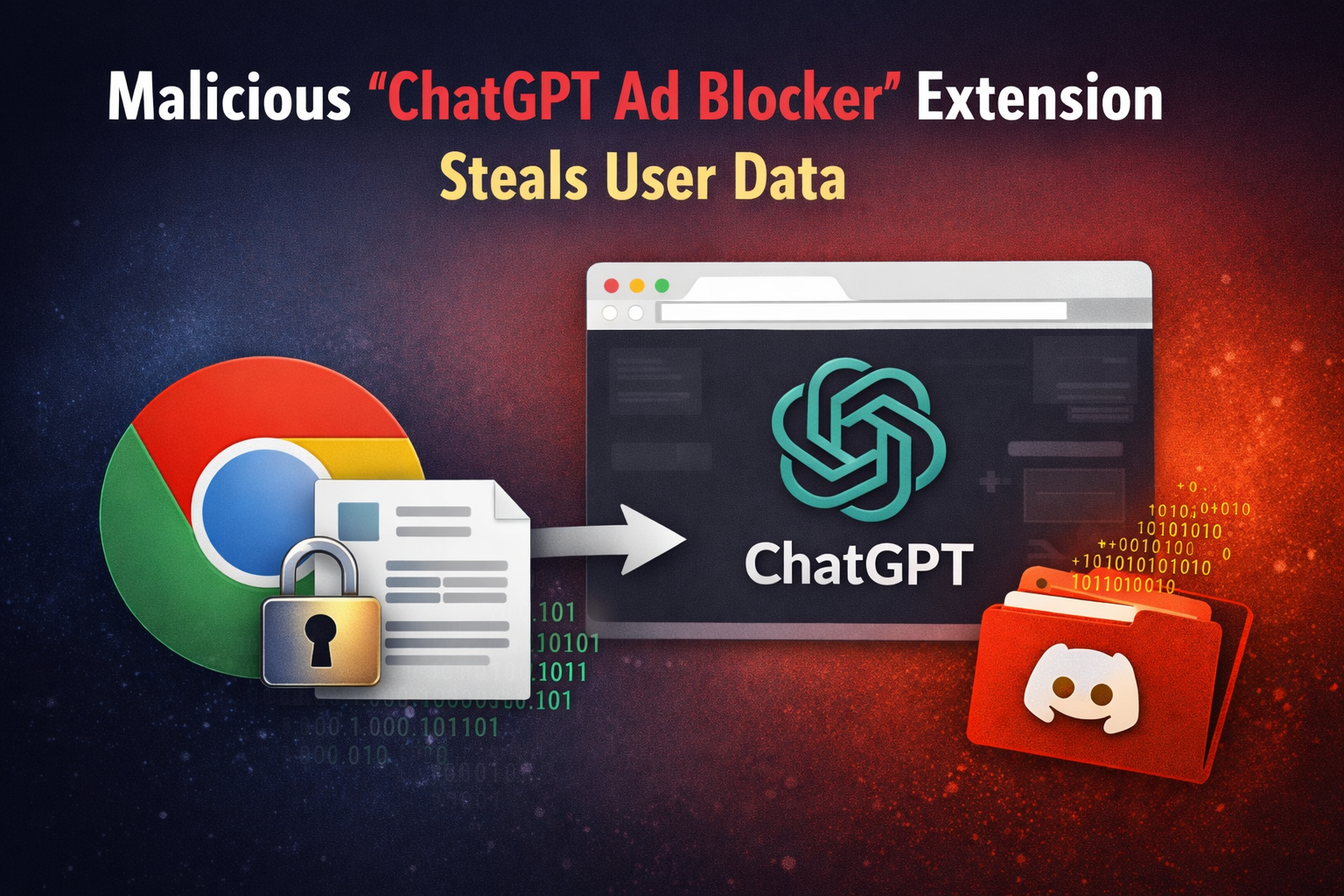
Security researchers have identified a rogue Chrome extension called “ChatGPT Ad Blocker” that secretly steals user conversations. It pretends to be a helpful tool designed to remove ads, but instead, it quietly collects sensitive data from ChatGPT sessions.
The extension takes advantage of user curiosity around ads in AI platforms, using a familiar name to appear trustworthy. Once installed, it monitors activity without interrupting the user experience, making it difficult to notice anything unusual.
It captures prompts, responses, and related metadata while continuing to behave like a normal extension on the surface.
Behind the Operation
After installation, the extension runs silently in the background and maintains persistence through scheduled activity. It regularly connects to a remote configuration hosted on GitHub, allowing attackers to change how it behaves without requiring any update from the user side.
When a user visits ChatGPT, the extension injects hidden scripts into the webpage. Instead of performing any ad-blocking function, it extracts the content of the page by removing styling and media elements while preserving the actual text of conversations.
This data is then compiled into a file and transmitted externally through a Discord webhook controlled by the attacker. The process is automated, meaning stolen conversations are continuously delivered without user awareness.
Investigators also observed suspicious activity linked to the developer account behind the extension. After years of inactivity, the account suddenly became active again, shifting focus toward JavaScript-based behavior. The same developer is connected to other AI-related services, raising broader concerns around data exposure.
Follow Us on:Linkedin, Instagram, Facebook to get the latest security news!
What This Means for Users
- Conversations on ChatGPT can be silently captured
- Prompts, responses, and session data are exposed
- Data is sent to external servers without visibility
- Remote control allows attackers to modify behavior anytime
- Associated services may carry similar risks
This incident shows how easily malicious tools can blend into everyday usage. Even simple extensions can operate quietly in the background while collecting valuable data.
Being cautious with browser extensions, especially those linked to popular platforms, is essential. Trust should not be based on names or claims alone, but on verified sources and transparency.




