
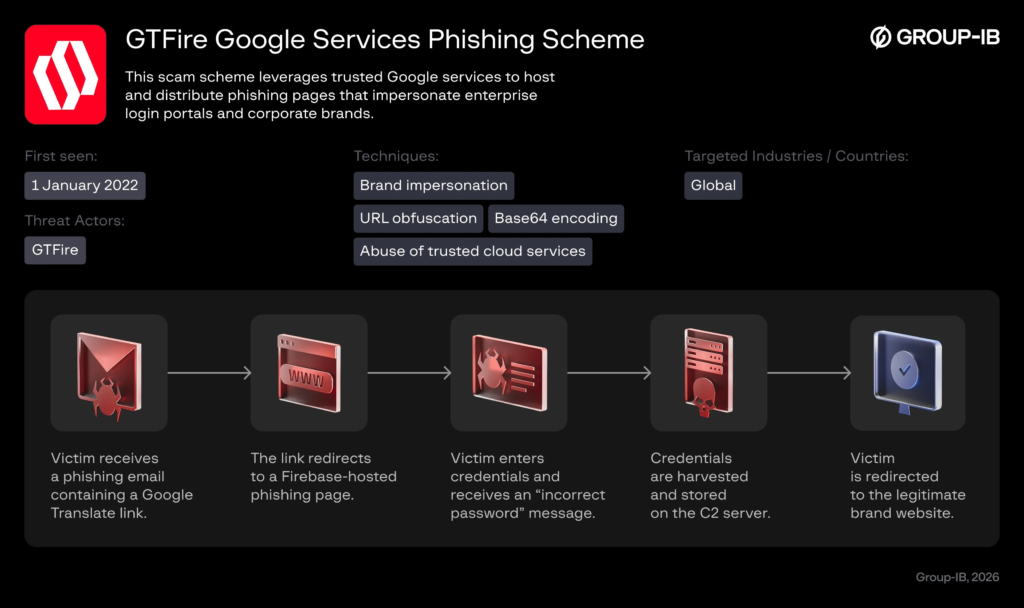
GTFire is a newly identified phishing campaign that misuses trusted Google services, including Firebase and Google Translate, to steal user credentials.
By hosting phishing content on legitimate Google-owned domains, the attackers are able to bypass many email security filters and web gateways. Because the links appear trustworthy, they are less likely to raise suspicion.
Victims are redirected to realistic login pages that imitate well-known brands. After entering their credentials, they are quietly sent to the real website, making the attack difficult to detect.
Global Impact and Scale
The campaign is widespread. Investigators uncovered attacker-controlled servers containing thousands of stolen credentials linked to more than 1,000 organizations across 100+ countries and over 200 industries.
Mexico has the highest number of confirmed victims, particularly in manufacturing, education, and government sectors. The United States, Spain, India, and Argentina are also significantly affected.
The use of trusted cloud services makes this campaign especially effective and harder to block using traditional security controls.
Group-IB researchers describe GTFire as a structured, large-scale credential theft operation.
Attackers reuse the same phishing templates across multiple brands and store stolen data on centralized servers, organized by date, language, and targeted servic
More than 120 phishing domains were discovered, using similar naming patterns to quickly rotate infrastructure and avoid detection.
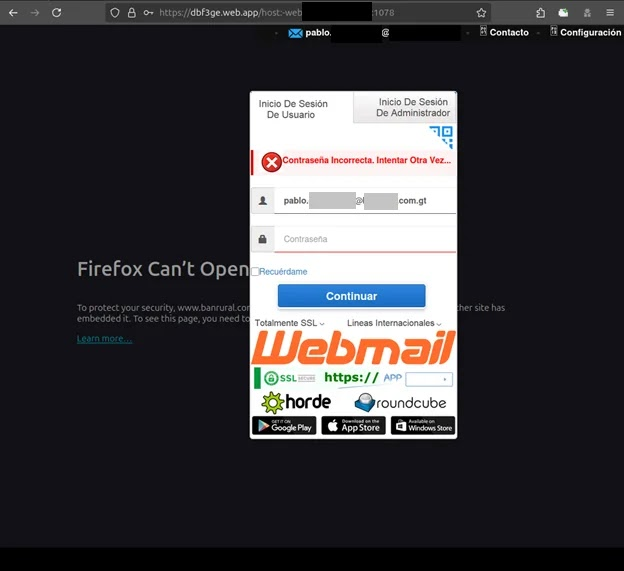
Attackers customize each fake login page to closely match real brands. After victims enter their credentials, they are redirected to the legitimate website, delaying suspicion.
Because the campaign uses trusted Google domains, traditional URL filtering and blocklists struggle to detect it — showing how easily legitimate infrastructure can be misused for phishing.
How the Attack Works
The attack starts with a phishing email that contains a Google Translate link. This link quietly routes the victim through Google’s translation service before redirecting them to a fake login page hosted on Firebase.
Because the link uses a Google domain, many email filters and web gateways do not block it.
Attackers create many random *.web.app subdomains to host phishing pages and rotate them frequently to avoid detection. Each page is designed to look like a real brand login portal.
When victims enter their credentials, they are shown a fake “wrong password” message and asked to try again. Both login attempts are secretly captured and sent to attacker-controlled servers, along with basic details like location and browser language.
The stolen data is collected using simple, ready-made backend tools, making the campaign easy to scale.
Mitigation Measures
Organizations should:
- Enforce phishing-resistant multi-factor authentication (MFA)
- Train employees to recognize suspicious Google-based links
- Monitor for unusual use of translate.goog and *.web.app domains
- Watch for brand impersonation hosted on trusted cloud platforms
- Share indicators of compromise with security communities and CERT teams
Trusted services can be misused, so detection strategies must go beyond basic domain reputation check




