
Researchers from Microsoft Security have spotted an upgraded version of the ransomware-as-a-service (RaaS) dubbed Hive.
Hive Ransomware
Hive was first detected in June 2021, with the data-encrypting software being offered to affiliates that pay to use the ransomware in their own campaigns. It also proves it’s one of the fastest evolving ransomware families, exemplifying the continuously changing ransomware ecosystem.
Microsoft noticed that Hive is not the first ransomware written in Rust, and follows in the footsteps of BlackCat.
Shift to a different and not common programming language
The change from GoLang to Rust makes this ransomware second threat family after the BlackCat that is written in this programming language. Malware gains additional benefits from this because memory safety gets improved and deeper control over low-level resources helps to evolve the infection. New malware versions now use a wide range of cryptographic libraries.
Changes to the variants that are Rust-based now mean that ransomware not only deletes backups to prevent easy file recovery, but the threat also goes for the file encryption differently:
Instead of embedding an encrypted key in each file that it encrypts, it generates two sets of keys in memory, uses them to encrypt files, and then encrypts and writes the sets to the root of the drive it encrypts, both with .key extension
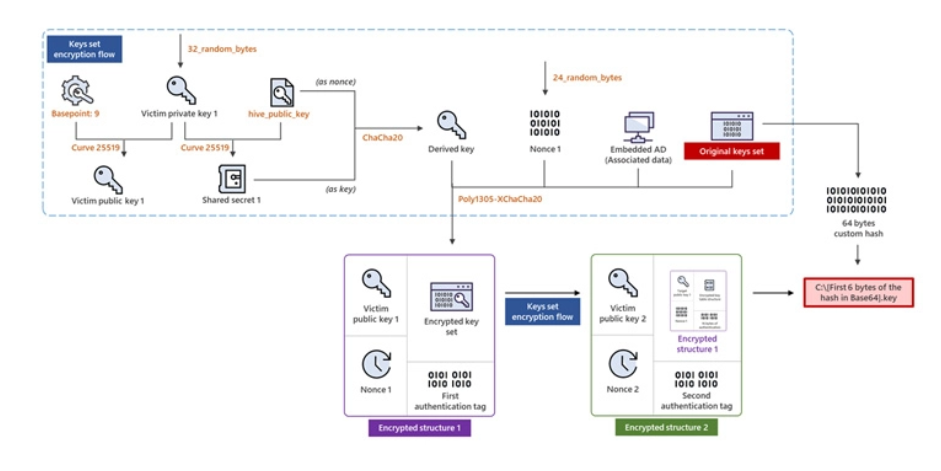
To determine which of the two keys is used for locking a specific file, an encrypted file is renamed to include the file name containing the key that’s then followed by an underscore and a Base64-encoded string (e.g., “C:\myphoto.jpg.l0Zn68cb _ -B82BhIaGhI8”) that points to two different locations in the corresponding .key file.
Recommended customer actions for Hive Ransomware
- Building credential hygiene
- Auditing credential exposure
- Prioritizing deployment of Active Directory updates
- Cloud hardening
- Enforce MFA
File Hash
- 44aba241dd3f0d156c6ed82a0a3a9e1
- 0f3e5603cf3f5cc91e8eb031a4b5c45d




