After Microsoft, FireEye and CrowdStrike, Malwarebytes hit by hacked SolarWinds.
Malwarebytes — UNC2452
An Anti-Virus provider for Microsoft Windows, macOS, Android, and iOS, which finds and removes malwares.
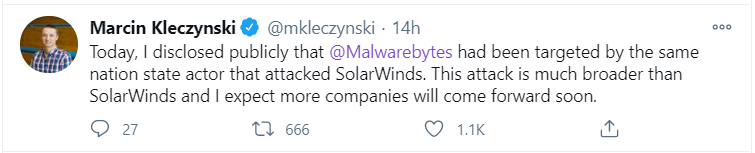
Yesterday, Marcin Kleczynski, CEO and Co-Founder of Malwarebytes, posted — hackers behind the SolarWinds breach also infiltrated Malwarebytes.
On December 15, the Microsoft Security Response Center informed Malwarebytes about suspicious activity.
From a third-party application in Malwarebytes Microsoft Office 365 tenant consistent with the tactics, techniques and procedures (TTPs) of the same advanced threat actor involved in the SolarWinds attacks.
“We immediately activated our incident response group and engaged Microsoft’s Detection and Response Team (DART)”, the CEO added.
At the time of auditing its Office 365 and Azure infrastructures for signs of malicious apps created by the SolarWinds hackers, also known in cyber-security circles as UNC2452 or Dark Halo.
“After an extensive investigation, we determined the attacker only gained access to a limited subset of internal company emails,” said Marcin Kleczynski.
Infected Products In Malwarebytes
Kleczynski said they also performed a very thorough audit searching for any signs of a similar compromise or past supply chain attack.
However, The hacker only gained access to a limited subset of internal company emails.
And also added that the “software remains safe to use.”
In short, Malwarebytes becomes the fourth major security vendor targeted by the SolarWinds threat actors.
Follow Us on: Twitter, Instagram, Facebook to get latest security news!
CrowdStrike has released a tool to help companies identify and mitigate risks in Azure Active Directory.