
Attackers are running a targeted espionage campaign across the Middle East by disguising malware as trusted messaging applications. The operation delivers an Android spyware known as ProSpy, aimed primarily at journalists, activists, and political figures.
Social Engineering and Delivery Tactics
The attack typically begins with direct contact. Victims are approached through platforms like LinkedIn, email, or messaging apps by accounts posing as journalists, support staff, or known contacts. These interactions are carefully crafted to build trust before introducing a malicious link.
The link is usually presented as something urgent or relevant, such as a video call request, shared document, or account alert. Once clicked, victims are redirected either to fake login pages or download portals.
Common tactics used:
- Impersonation of trusted individuals or organizations
- Spearphishing messages tailored to the target
- Fake login pages mimicking services like email or cloud platforms
- Malicious download links disguised as secure communication tools
This approach relies heavily on human trust rather than technical exploitation, making it highly effective even against cautious users.
Fake Apps and Spyware Capabilities
The core of the campaign is the use of fake Android applications that appear to be secure messaging tools. These apps are distributed through convincing websites that mimic official sources and offer “enhanced” or “pro” versions of popular platforms.
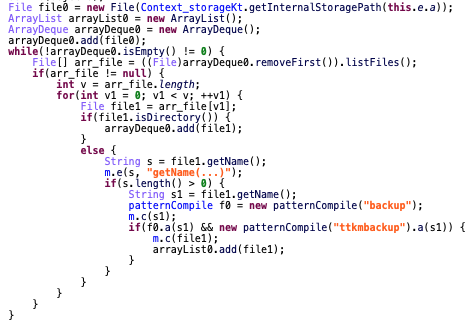
Once installed, the spyware operates silently in the background, collecting and transmitting sensitive data to attacker-controlled servers.
Key capabilities include:
- Access to contacts, messages, and call-related data
- Collection of device information and stored files
- Extraction of documents, media, and backup data
- Continuous communication with remote command servers
The malware is designed to blend in as a legitimate app, making detection difficult for users who install it outside official app stores.
Follow Us on:Linkedin, Instagram, Facebook to get the latest security news!
Broader Implications
This campaign highlights a growing trend where attackers combine social engineering with mobile spyware to conduct surveillance operations. The targeting of civil society groups suggests a shift toward more personalized and contract-driven espionage activities.
It also reinforces a critical point: even advanced threats often rely on simple entry points — convincing a user to trust and install something that appears legitimate.




