
Researchers at Guardio Labs have uncovered a large and highly organized phishing operation known as AccountDumpling, which has already compromised more than 30,000 Facebook accounts worldwide. What makes this campaign stand out is not just its scale, but the way it abuses legitimate platforms to make phishing emails appear completely authentic.
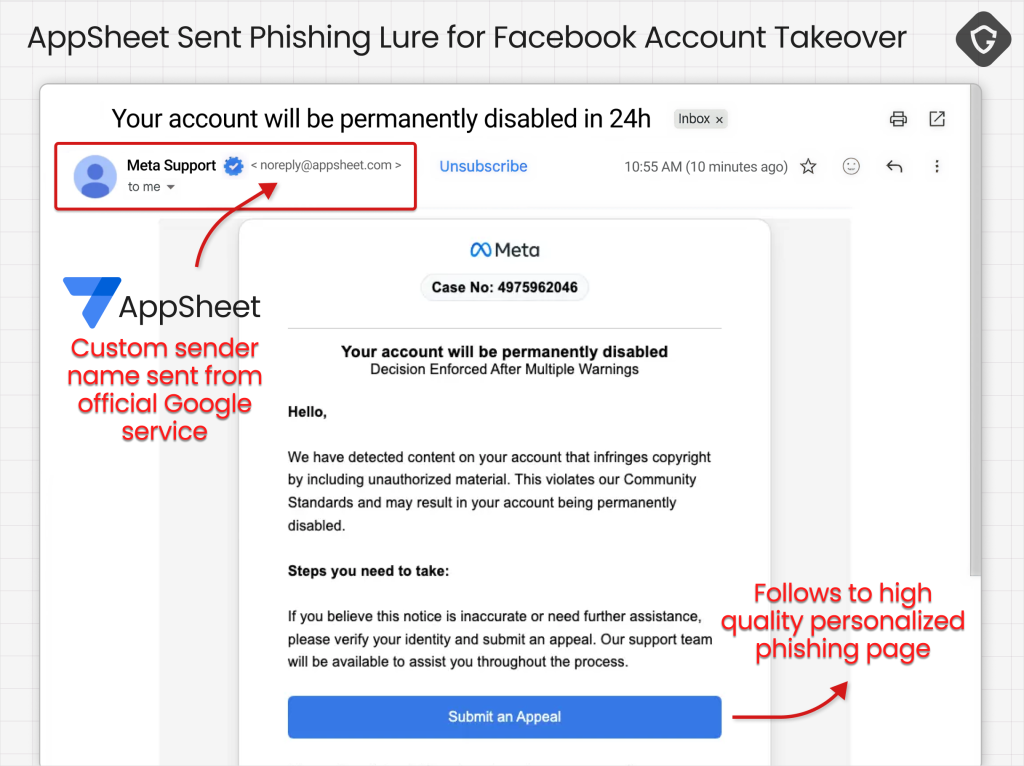
Instead of relying on fake domains or compromised mail servers, attackers use Google AppSheet to send emails through Google’s own infrastructure. These messages are generated as part of automated workflows, meaning they pass authentication checks like SPF, DKIM, and DMARC without raising suspicion.
As a result, security tools and spam filters see them as trusted communications, allowing phishing messages to land directly in inboxes of targeted users—often business account owners managing Facebook pages.
Multi-Layered Attack Strategy
The campaign is not a single phishing page but a structured, multi-stage system designed to increase success rates. Victims are first directed to pages hosted on Netlify, where attackers replicate the Facebook Help Center with high accuracy. These pages are customized per victim using unique subdomains, making them difficult to block using traditional security measures.
From there, users are guided through a series of steps that collect not only login credentials but also deeper identity information such as date of birth and even government-issued ID images. In some cases, the attackers shift tactics by offering fake incentives, like verification badges, hosted on platforms such as Vercel. These pages are designed to look dynamic and legitimate, while quietly bypassing detection systems using techniques like hidden Unicode characters.
The operation becomes more advanced in later stages. Attackers host phishing documents on Google Drive, presenting them as official Meta notifications. These documents, often designed using Canva, contain embedded links that redirect victims into interactive phishing environments. These environments are powered by real-time communication frameworks, allowing attackers to actively engage with victims during the login process.
This live interaction is a critical aspect of the campaign. Instead of passively collecting credentials, attackers can request one-time passwords, monitor user actions, and even capture browser sessions as they happen. This significantly increases the likelihood of successful account takeover, even when multi-factor authentication is enabled.
Real-Time Data Exfiltration and Attribution
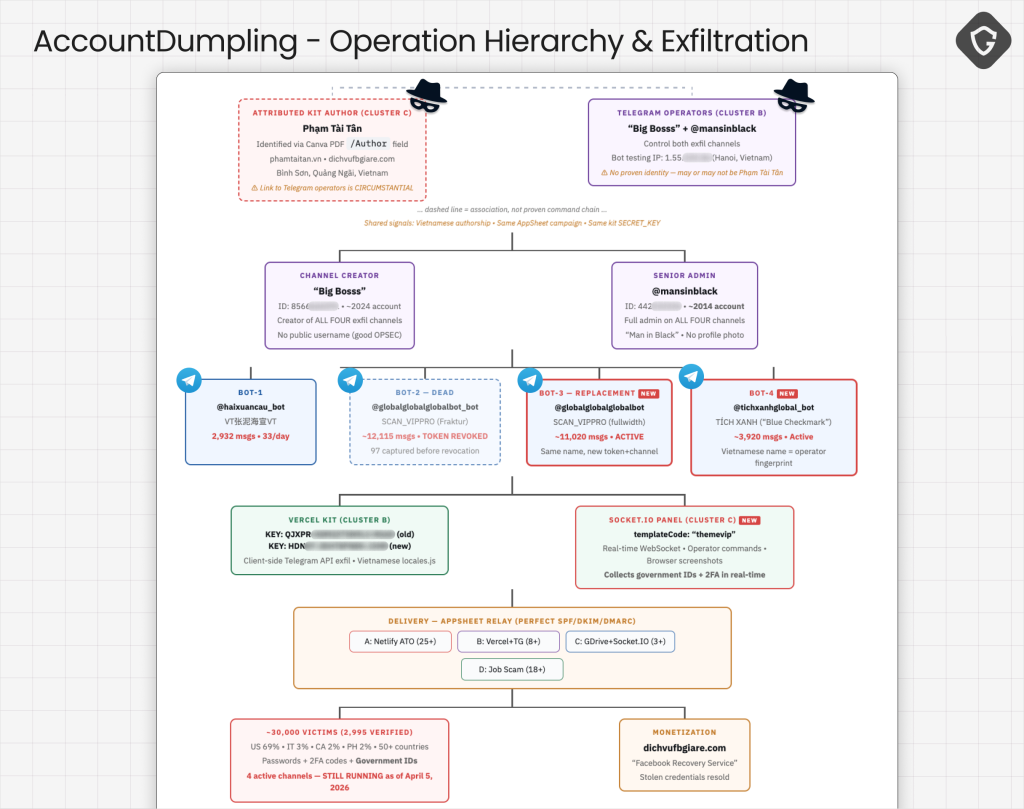
Once credentials are captured, they are immediately transmitted through a centralized system built around Telegram bots. This allows operators to monitor incoming data in real time and quickly take control of compromised accounts before victims notice suspicious activity.
Analysis of the infrastructure shows a strong operational scale, with thousands of records flowing into attacker-controlled channels. Most victims are concentrated in regions like the United States and Europe, indicating a focus on high-value targets such as businesses and influencers.
Investigators were also able to trace elements of the campaign back to Vietnamese actors. This attribution is supported by metadata found in phishing documents and developer comments embedded within the malicious code, providing insight into the origin of the operation.
A Shift Toward Industrialized Phishing
AccountDumpling reflects a broader shift in cybercrime, where phishing is no longer a simple tactic but part of a larger, industrialized ecosystem. Attackers are combining trusted services, automation, and real-time interaction to create highly effective campaigns that are difficult to detect and disrupt.
Compromised accounts are rarely the end goal. They are often reused for further scams, advertising fraud, or additional phishing attacks, creating a cycle that sustains and expands the operation. This approach shows how modern threat actors are leveraging legitimate platforms at scale, turning them into tools for widespread abuse while staying under the radar.




