
A multistage remote access trojan (RAT) named ZuoRAT has been targeting remote workers with the help of small office/ home office (SOHO) routers across North America and Europe since 2020.
ZuoRAT Malware
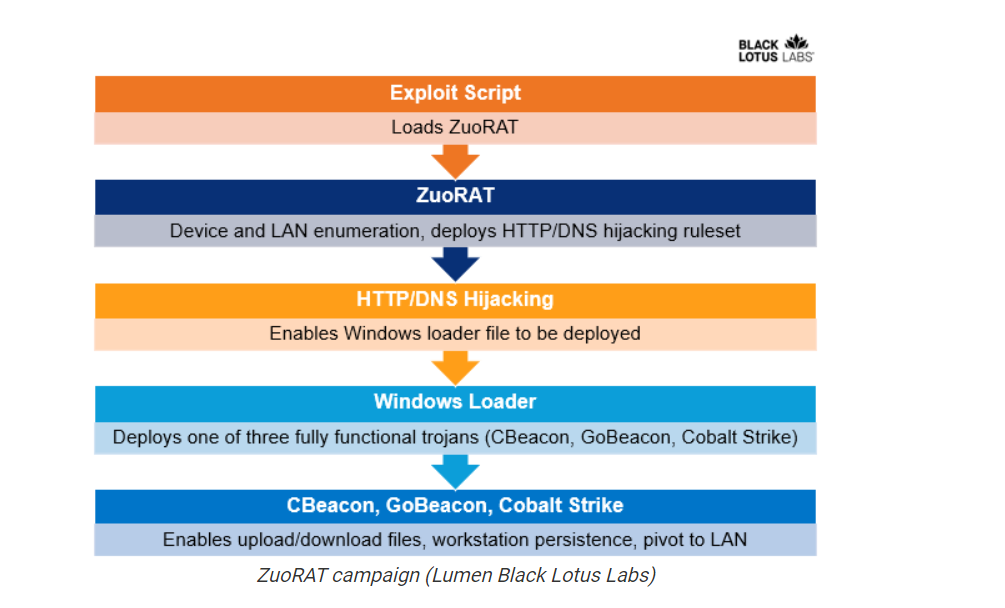
The malware known as ZuoRAT, makes its way onto routers through exploits for known vulnerabilities. It can also infect other devices in the network and introduce additional malware via DNS and HTTP hijacking.
ZuoRAT is a MIPS file compiled for SOHO routers that can enumerate a host and internal LAN, capture packets being transmitted over the infected device, and perform person-in-the-middle attacks.
Two more custom trojans were delivered onto hacked devices during these attacks:
one C++ based one named CBeacon targeting Windows workstations and a Go-based one dubbed GoBeacon that could likely infect Linux and Mac systems besides Windows devices.
A first-stage RAT developed for SOHO routers which we dubbed ZuoRAT,based on the Chinese word for “left.
The researchers estimate that the campaign has so far impacted at least 80 targets. They warn that organizations should keep a close watch on SOHO devices and look for any signs of malicious activity.
In order to mitigate the threat, the firms must ensure patch planning includes routers, and confirm these devices are running the latest software available.
File Hash
- 9b07d1b4acaaed080c5e68411b907269
- 127ccc1b4363eb1639af1baf372984e3
- 800c2822450a33c3b879f9f51dbdd98a
Follow us for more, Facebook, Twitter, LinkedIn and Instagram




