
A new web3 technology is being abused widely by threat actors, according to security researchers from tech giant Cisco.
What is IPFS ?
The InterPlanetary File System (IPFS) is a protocol and peer-to-peer network for storing and sharing data. It is designed to enable decentralized storage of resources on the internet. It was built to be resilient against content censorship, meaning that it is not possible to effectively remove content from within the IPFS network once it’s stored there.
This includes Dark Utilities, a command-and-control (C2) framework that’s advertised as a way for adversaries to avail remote system access, DDoS capabilities, and cryptocurrency mining, with the payload binaries provided by the platform hosted in IPFS.
Cisco Talos has observed multiple ongoing campaigns that leverage the IPFS network to host their malware payloads and phishing kit infrastructure while facilitating other attacks.
However, researchers with Cisco Talos said that this legitimate use also makes it harder for security teams to sniff out malicious IPFS activity. This has been a driving factor behind a growing volume of malware samples – including Hannabi Grabber and Agent Tesla – in attacks this year that leverage IPFS.
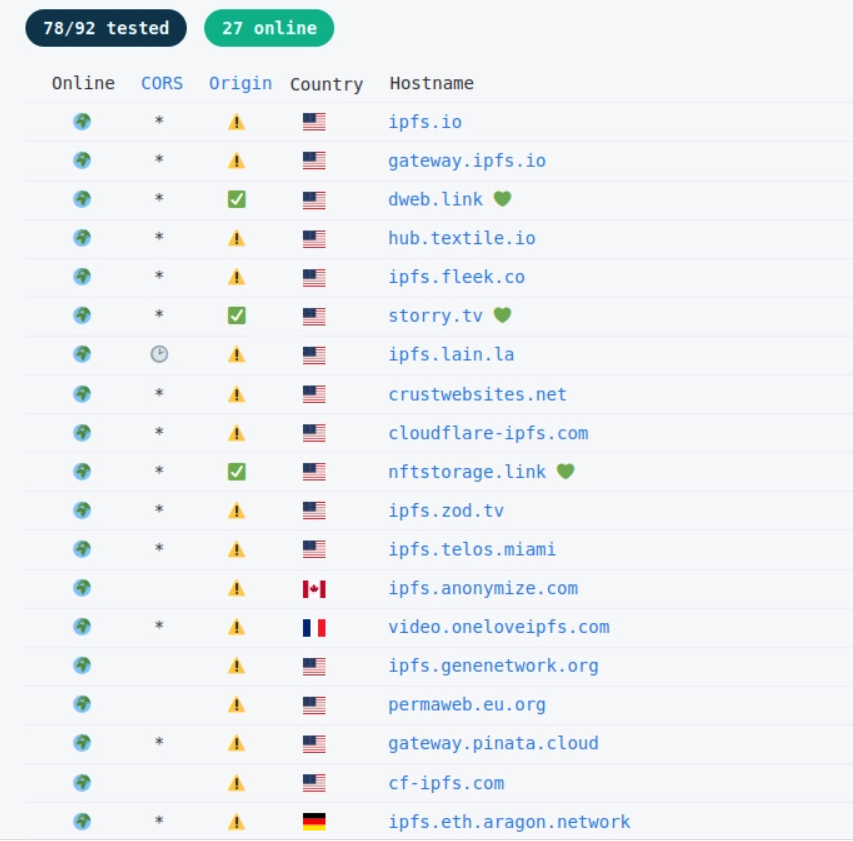
Resources stored within IPFS can be accessed using an IPFS client or by building an IPFS “gateway” using publicly available tools. Any computer can download the IPFS software in order to start hosting and serving files, and because of this ease of use, coupled with challenges around the moderation of IPFS hosted content, IPFS is lucrative for attackers, said researchers.
In one campaign that Talos researchers observed, the attacker sent victims a phishing email with a ZIP attachment containing a malware dropper in the form of a PE32 executable. When run, the downloader would reach out to an IPFS gateway and retrieve a second-stage malware payload hosted on the peer-to-peer network. The attack chain ended with the Agent Tesla remote-access Trojan getting dropped on the victim’s system.
Brumaghin said that attackers will continue to close in on new technologies that are related to the emerging concept of the distributed web, also referred to as Web3.
IOCS
3607ad99e031e5f5cfc93fc0886f0b79d6bcec5b8ed341beb9aadf1433fe8877
422ef98bf095435e5875a22607cd949b7befbee6cd800604145dd00ca44748d2
4e2d0315759262210266e77b3adff7ea3bf02e24f3a585c177d648d4ab20e0cf
7abeb65b5ca90bb2963d1eddb2c1ca3663aa0c8eb4401be375a429e98c36b1c9
9231bc7c1c33e51e0794e5f2364edc54be39160d48235bc74edac3b34a6cb41a
9eed6f3d692496d1bc0cfde4632a069585cd3dfa20af05ade322326a17c6eda9
a6ead3b89944a4f8b1a2c28d669c4e0029101c2f15600b8071bb6cc30a29e698
b0cb0be1dd30b6de83b2d5c7b91b21a0cb98f95ac4b2eebcc80b8efc688b2295
bf35e7ee59cf81f74be092d43acbb711377f115426db8e9f6f45fa1bbb3086b7
c092c2a4bc5f4587b4631b773aedaae59048002e59280e8c3448c8073f14a37e
c1beb3da95b1d28e3dbc2a192cbef0737e32fd75023da55d4dfa8d80d4f11463
c2f66871aeed4da97fb75a3d753bf3349257a5028a7c7a27ce043301d1bbc9a4
c35ddc08b1708ce739bbb96d5ace6bdec5bb0bc51533ac83fc88499bfe24b585
c7778e2be8b71fb75b9e53b651d17d7cdf3e25b6128fdd23224c582f08e5f72e
d8e16aa541f4c978f49126b25b8dd1efe19d51f9e92613e56dad1580036c2b0e
e311e522fc0a361a3f04e6594b1199f8fc1ccb01a390d0dd67f260969ca026cf
e7c3b0ad59ca932e4c293d3e76bd0c18a9d8b96b6bff5c88d917169b5f00b673
f844fee4de0dc8c0aa88c06a287db928aa307d804a1b630acf504f2192a7007f
138.201.103.170
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!




