Microsoft to fix Windows 10 bug that can corrupt a hard drive just by opening a folder or just by looking at an icon.
NTFS Hard Drive Corrupt
A bizarre Windows 10 bug that could corrupt a hard drive just by looking at an icon.
Security Researcher Jonas L, revealed the details and described as “nasty vulnerability“.
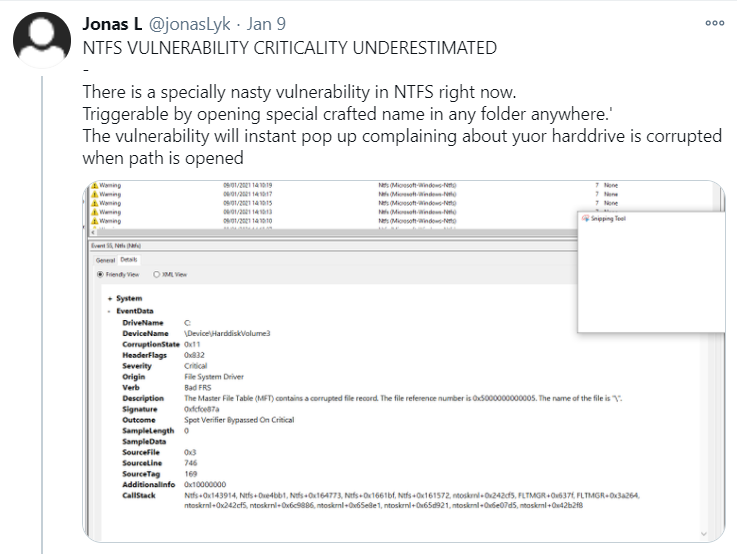
He further added, the bug could be hidden in any form:
- ZIP file,
- a folder,
- or, even a Windows shortcut.
If the ZIP file is extracted or the file is opened, or simply look at a folder the bug will be activated and corrupt the hard drive.
Follow Us on: Twitter, Instagram, Facebook to get latest security news!
Working:
According to Will Dormann, vulnerability analyst this NTFS corruption has been around since the Windows 10 1803 update that was released back in 2018.
Bleeping Computer explains — running the command cd c:\:$i30:$bitmap will essentially destroy a drive (so don’t do it!).
Also, Jonas found — if a shortcut file was created with its icon location — C:\:$i30:$bitmap, merely opening the folder containing this file is enough to corrupt a drive.
The bug also doesn’t require admin rights to trigger or special write permissions.
And, affected Windows 10 users will be asked to reboot their PC to repair the corrupted disk records.
The reboot will trigger the Windows chkdsk process, which should successfully repair the corruption.
However here, it could make it more problematic for IT admins if chkdsk fails to automatically repair affected drives.
Siam Alam, security researcher demonstrated yet another way to trigger drive corruption:
Security Recommendations:
In short, Microsoft is aware of the issue affecting the $i30 NTFS attribute, a fix has yet to be produced.
However, of course, there are various ways — malicious shortcuts could be implemented on a computer, and trick the user into opening its containing folder.
The use of this technique relies on social engineering and as always we encourage our customers to practice good computing habits online, including exercising caution when opening unknown files, or accepting file transfers.”







