Security researchers have discovered a GhostClaw malware has been discovered in a malicious npm package that steals developer credentials and sensitive system data.
Instead of installing a normal utility, the package secretly deploys a powerful infostealer and remote access tool on the developer’s machine.
The malware operation, known as GhostLoader, is designed to steal sensitive data such as SSH keys, cloud credentials, browser sessions, and other developer secrets.
How the Attack Works
The package appears harmless during a quick inspection. It includes a clean configuration file and simple source code, making it look like a normal installer.
However, the attack starts during installation through a hidden script that automatically installs the tool globally. When the developer runs the openclaw command, a fake CLI installer appears with progress bars, while the malware quietly connects to attacker-controlled servers.
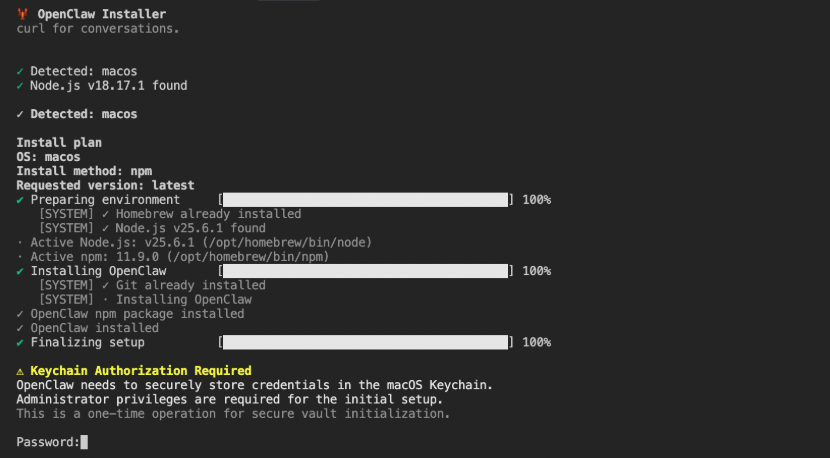
During this process, the script may display a fake system prompt asking for the user’s password, claiming it is required to store credentials securely.
GhostLoader Malware
Once the password is entered, the malware downloads an encrypted second stage called GhostLoader.
This malware installs itself as a hidden service named npm telemetry and creates persistence on the system using methods such as:
• modifying shell configuration files
• creating cron jobs or background tasks
• launching hidden monitoring processes
This allows the malware to remain active even after system reboots.
Data Theft Capabilities
The malware focuses heavily on developer environments and attempts to steal valuable data including:
• SSH keys and Git credentials
• cloud credentials for AWS, Azure, and GCP
• Docker and Kubernetes configuration files
• browser cookies and saved passwords
• cryptocurrency wallet data
It can also collect AI-related configuration files and developer project information.
Protection and Mitigation
Security teams recommend installing packages only from trusted sources and carefully reviewing npm packages before use.
Developers who installed the malicious package should immediately remove it, delete persistence files, and consider rebuilding the affected system due to the depth of the compromise.
This campaign highlights how attackers are increasingly targeting developers by abusing trust in open-source package ecosystems.
Indicators of Compromise
| Indicator | Value |
|---|---|
| Package Name | @openclaw-ai/openclawai |
| Package Type | NPM |
| Versions | 1.5.15,1.5.14 |
| XRAY-ID | XRAY-949975 |
| C2 Domain | hxxps\[://\]trackpipe\[.\]dev |
| Bootstrap Path | /t/bootstrap?t=fafc0e77-9c1b-4fe1-bf7e-d24d2570e50e |
| Campaign ID | complexarchaeologist1 |
| Install Directory | ~/.cache/.npm_telemetry/ |
| Executable Name | monitor.js |
| Temp File Pattern | /tmp/sys-opt-*.js |
| Shell Hook Comment | # NPM Telemetry Integration Service |
| Cron Comment | # Node.js Telemetry Collection |
| Encryption | AES-256-GCM (16-byte IV, 16-byte auth tag) |
| Geo Lookup | hxxps\[://\]ipinfo\[.\]io/json |
| File Upload Fallback | GoFile.io API |
| Exfiltration | Telegram Bot API, C2 panel upload |
| Environment Variables | NODE_AUTH_TOKEN, NODE_CHANNEL, NPM_CONFIG_TAG, GHOST_RECOLLECT, GHOST_TG_CONFIG |