The Lazarus Group is actively using ClickFix-style social engineering to deploy a new macOS malware framework called “Mach-O Man.” Instead of exploiting vulnerabilities, the attack relies on user interaction, making it highly effective against modern defenses.
This activity has been closely analyzed by Mauro Eldritch, who has documented how this campaign is impacting high-value macOS users, especially in fintech and crypto sectors.
Initial Access and Social Engineering Flow
The attack typically begins with targeted outreach on Telegram, where threat actors impersonate trusted contacts such as colleagues or business partners. Victims—often executives or developers—receive urgent meeting requests designed to trigger quick action.
They are then redirected to phishing pages that closely resemble platforms like Zoom, Microsoft Teams, or Google Meet. These pages claim a technical issue and instruct the user to fix it manually.
Instead of a traditional exploit, the victim is guided to copy and execute a Terminal command. Because this action is user-initiated, many security tools interpret it as legitimate behavior.
Execution Chain and Malware Behavior
Once the command is executed, the infection chain unfolds in multiple stages designed to blend in with normal macOS activity.
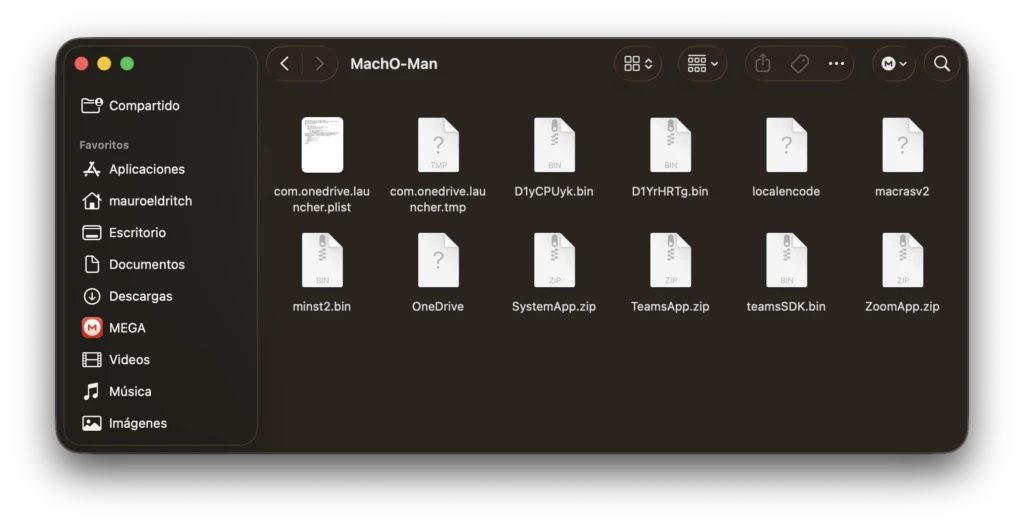
- The first-stage binary (commonly seen as teamsSDK.bin) acts as a downloader that retrieves additional components
- Fake macOS applications are dropped, mimicking meeting tools or system prompts to appear legitimate
- These apps repeatedly request user passwords, often using poorly written prompts to trick the victim
- A secondary module (such as D1YrHRTg.bin) performs deep system profiling using native tools like sysctl
The profiling stage gathers extensive system intelligence, including host identifiers, operating system details, running processes, network configuration, and browser-related data from Chrome, Safari, Brave, and similar applications.
Interestingly, researchers observed flaws in parts of the malware. Some profiling components enter continuous loops, repeatedly sending the same data to command-and-control infrastructure, which can cause noticeable performance issues on infected machines.
To avoid execution barriers, the malware leverages macOS utilities like codesign to apply ad-hoc signatures, helping malicious binaries run under standard policies without raising immediate suspicion.
Credential Theft and Data Exfiltration
The final stage of the attack is handled by a stealer component referred to as macrasv2. This module focuses on extracting high-value data from the compromised system.
Targets include:
- Browser-stored credentials and active session cookies
- macOS Keychain entries containing saved secrets
- Files that can grant access to SaaS platforms, internal systems, or crypto wallets
All collected data is compressed into archive files (for example, user_ext.zip) and exfiltrated to attacker-controlled servers.
Persistence Mechanism
To maintain long-term access, additional components like minst2.bin are deployed. These create persistence by placing disguised binaries—often pretending to be legitimate services like OneDrive—inside directories labeled as security-related (such as an “Antivirus Service” folder).
The malware then registers itself as a LaunchAgent, ensuring execution every time the user logs in.
Why This Campaign Is Effective
This attack stands out because it avoids traditional exploitation techniques. By relying on user-executed commands and built-in macOS tools, the activity appears normal to many EDR solutions until after credentials and access tokens are already compromised.
For organizations where macOS devices are widely used—especially among developers and leadership—this creates a serious risk. A single compromised system can lead to broader access across internal infrastructure and financial assets.
Detection and Defensive Considerations
To counter this type of campaign, defenders need to shift focus toward behavior rather than just exploits.
- Monitor unusual Terminal activity and command execution patterns
- Identify and block ClickFix-style phishing workflows
- Regularly audit LaunchAgents for suspicious or disguised entries
- Track outbound connections to uncommon ports or Telegram-related infrastructure
- Use sandbox environments like ANY.RUN to safely analyze suspicious files, URLs, and execution chains
Interactive sandboxing plays a key role in understanding how these multi-stage attacks operate, allowing defenders to reconstruct the full infection path and extract indicators for detection.




