Malicious npm Package Targets Developers With GhostClaw Malware
Security researchers have discovered a GhostClaw malware has been discovered in a malicious npm package that steals developer credentials and sensitive system data.Instead of installing a normal utility, the package [...]
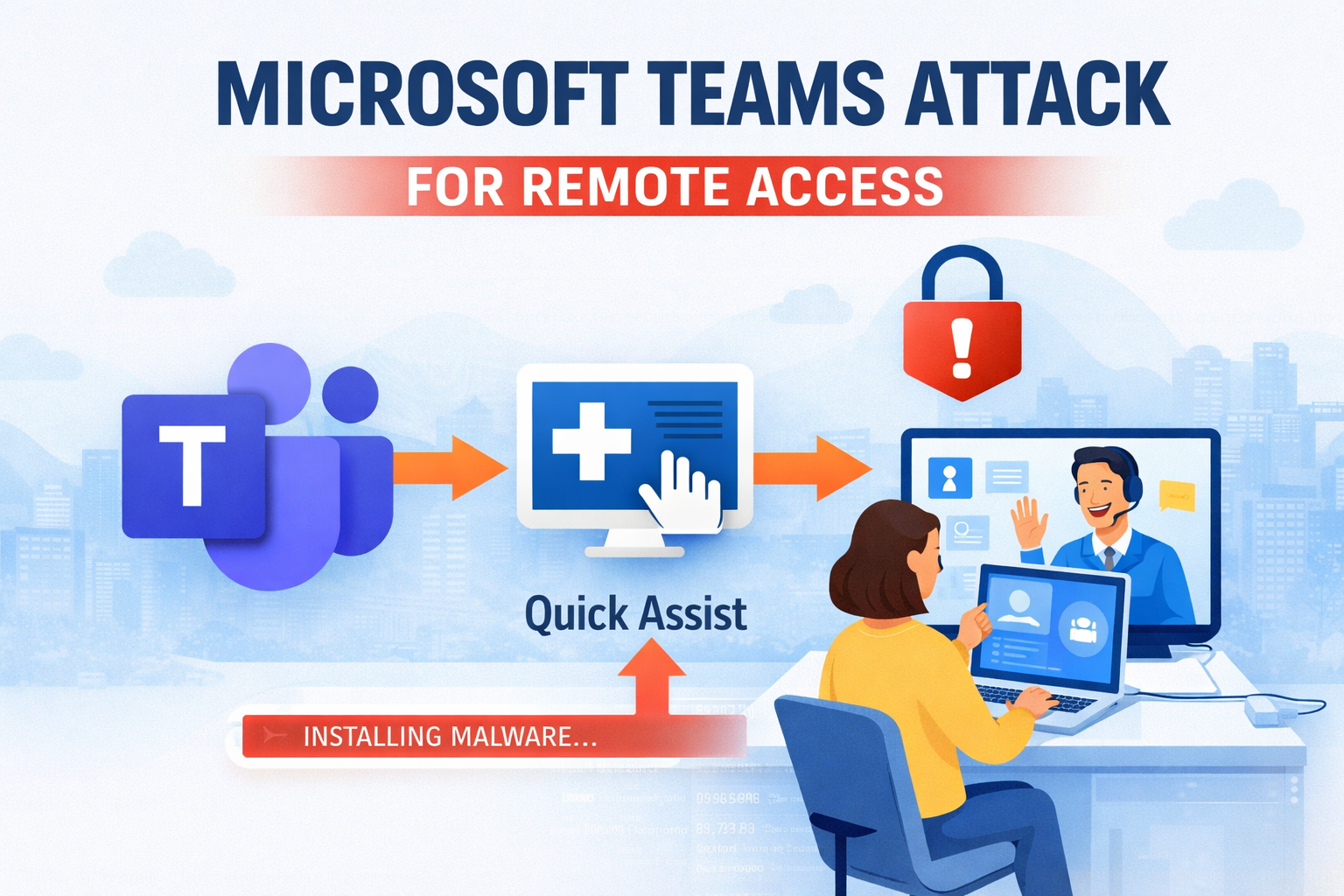
Hackers Use Microsoft Teams Attack Method to Gain Remote Access
Cybersecurity researchers have uncovered Microsoft Teams attack campaigns are now targeting employees in finance and healthcare organizations by posing as internal IT support. In this operation, attackers pretend to be [...]
Critical ZITADEL XSS Vulnerability Could Enable Full Account Takeover
A critical security vulnerability has been discovered in ZITADEL, an open-source identity and access management platform used by many organizations for authentication and access control. The vulnerability, tracked as CVE-2026-29191, [...]
OpenAI Codex Improves Automated Security Fixes
OpenAI has introduced Codex Security, a new AI-powered application security agent that helps developers automatically detect and fix vulnerabilities in code. Previously known as Aardvark, the tool is now available [...]
Apache ActiveMQ Vulnerability Enables DoS Attacks
Researchers have identified a security issue in Apache ActiveMQ, specifically related to the Apache ActiveMQ DoS vulnerability, a widely used open-source message broker that enables communication between applications. The vulnerability, [...]