Mirai botnets are rapidly evolving into powerful platforms used for large-scale DDoS attacks and proxy abuse across IoT and mobile devices.
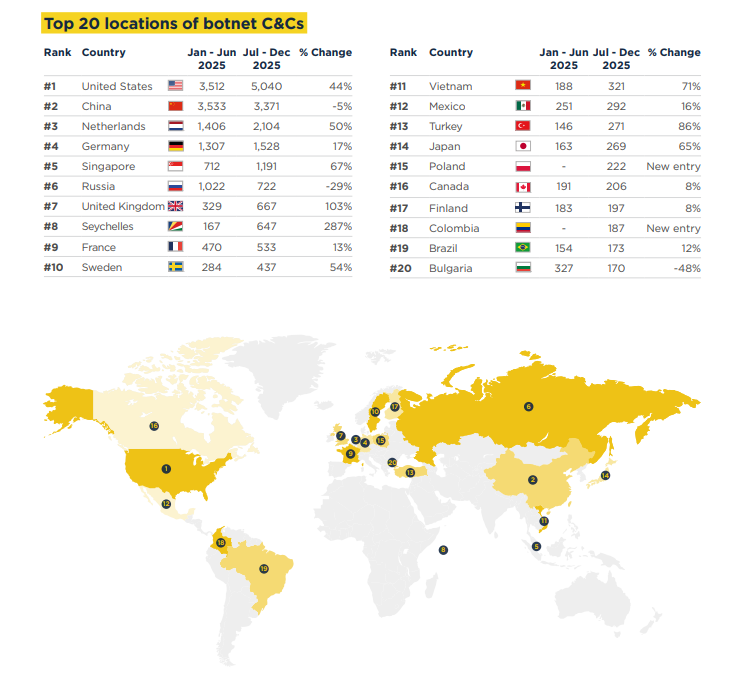
Researchers observed over 21,000 command-and-control (C2) servers between July and December 2025. Along with this growth, attackers are increasingly using infected devices as residential proxies, not just for DDoS attacks.
This rise also aligns with a surge in massive DDoS campaigns. Reports highlight “hyper-volumetric” attacks, including one reaching 31.4 Tbps, showing how far these botnets have evolved. At the same time, botnet activity has sharply increased after a period of stability, indicating a renewed wave of large-scale operations.
Evolution of Mirai-Based Botnets
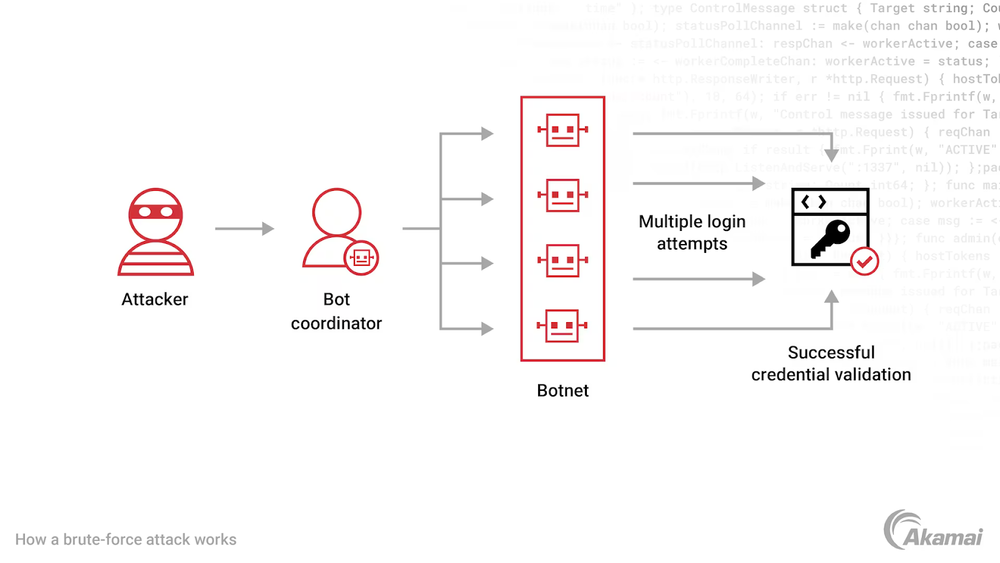
Mirai first appeared in 2016, targeting internet-connected devices such as routers and IoT systems that often rely on weak or default credentials. Once compromised, these devices are added to a botnet that can launch high-volume traffic floods across multiple layers.
The public release of Mirai’s source code played a major role in its growth. It allowed attackers to create multiple variants, each adding new capabilities while keeping the core attack techniques intact.
One well-known variant, Satori, rapidly spread by exploiting vulnerabilities in routers, especially through command injection flaws. It used automated scripts to download and execute malware across different device architectures, allowing infections to scale quickly without user interaction.
Expanding Capabilities and Abuse Techniques
Modern Mirai botnets are no longer limited to DDoS attacks. They are now being used in more advanced and flexible ways, increasing their overall impact.
Key capabilities seen in recent campaigns include:
- Large-scale DDoS attacks reaching record-breaking volumes
- Use of infected devices as residential proxy networks
- Automated exploitation of IoT vulnerabilities
- Multi-architecture malware deployment for wider coverage
- Stealthier operations to avoid detection
Aisuru-Kimwolf Expanding DDoS and Proxy Abuse
Newer botnet families like Aisuru and Kimwolf have taken Mirai-based threats to the next level. These botnets are now used not only for massive DDoS attacks but also as residential proxy networks that can be rented for cybercrime activities.
Security reports have linked Aisuru-Kimwolf to extremely large attacks, including one reaching 31.4 Tbps. These attacks often generate massive traffic with billions of packets per second, using random patterns to avoid basic detection and filtering systems.
At the same time, Kimwolf, which targets Android devices, is being used to exploit residential proxy services. Attackers use these networks to access internal systems, infect devices like smart TVs and smartphones, and then sell that access for activities such as fraud and credential stuffing.
Ongoing Threat and Defensive Focus
Law enforcement and tech companies have started taking action against these botnets by targeting their command-and-control infrastructure and disrupting the platforms used to manage proxy networks.
However, these efforts have not fully stopped the threat. Mirai-based botnets continue to survive and grow because many devices remain unpatched, especially routers and Android systems. Attackers can also quickly rebuild their infrastructure after disruptions.
For defenders, the focus should remain on strong basic security practices:
- Keep routers and IoT devices updated
- Monitor unusual outbound traffic
- Secure Android and edge devices
- Track indicators linked to Mirai variants
As these botnets continue to evolve, they are becoming more powerful and more versatile, combining large-scale disruption with stealthy abuse of network access.