
Exfiltrator-22 is a new post-exploitation kit that can spread ransomware undetected. Researchers speculate that the creators of this kit are former LockBit 3.0 affiliates, experts in anti-analysis and defense evasion.
Cybercriminals advertise it for $1,000 per month and $5,000 for lifetime access. After paying, clients receive access to a dashboard on a strong VPS (virtual private server) in order to control the malware and send commands.
New Exfiltrator-22 post-exploitation kit
The first version of Exfiltrator-22 (EX-22) appeared on November 27, 2022, and about 10 days later, its authors created a Telegram channel to promote it to other cybercriminals.
By January 2023 the kit was 87% ready and up for sale, searching for affiliates. On February 10, 2023, the threat actors behind it posted two YouTube videos that showed its lateral movement and ransomware-spreading features.
What are their features?
EX-22 has many features in common with similar tools but additional features that encourage ransomware development and data theft.
- Create a reverse shell with elevated privileges access.
- Download files from the endpoint to the C2 or upload files to the compromised system.
- Use a keylogger to record keystrokes.
- Launch a ransomware program to encrypt data on the compromised system.
- Take screenshots of the victim’s PC screen.
- To gain immediate access to the compromised computer, launch a live VNC (Virtual Network Computing) session.
- Gain greater control over the infected gadget.
- Create continuity between system reboots.
- Use a worm module to propagate the malware to additional computers connected to the same network or the open internet.
- Exfiltrate data out of the LSAAS (Local Security Authority Subsystem Service).
- Create cryptographic hashes of the victim’s files to keep track of file locations and content modification.
The above commands are sent to the compromised systems via the Windows console program ‘EX22 Command & Control’. The results from the commands are then returned to the command and control server and displayed directly in the console application.
Through the service’s web panel, cybercriminals can also set scheduled tasks, update agents to a new version, change the composition of a campaign or create new ones.
CYFIRMA researchers discovered links between the Exfiltrator-22 kit and LockBit 3.0 affiliates or members of the ransomware gang. The post-exploitation kit has even the same C2 infrastructure as LockBit 3.0.
IOCS
| 874726830ae6329d3460767970a2f805 |
| eca49c8962c55bfb11d4dc612b275daa85cfe8c3 |
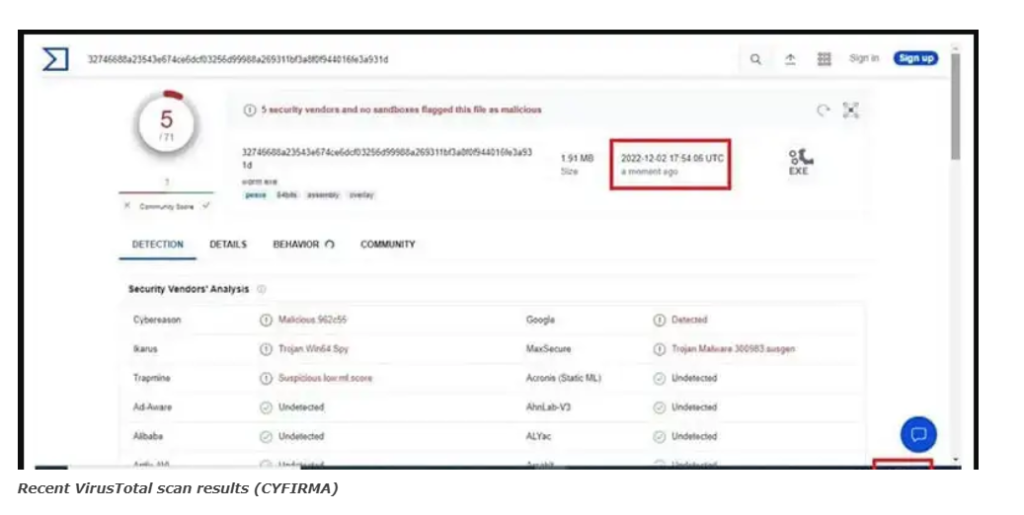
| 32746688a23543e674ce6dcf03256d99988a269311bf3a8f0f944016fe3a931d |
| Worm[.]exe |
| Worm24[.]exe |
| 23.216.147[.]76 |
| 20.99.184[.]37 |
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!




