
The threat actor behind the attacks on Twilio and Cloudflare earlier this month has been linked to a broader phishing campaign aimed at 136 organizations that resulted in a cumulative compromise of 9,931 accounts.
Okta Hackers
Now, cybersecurity company Group-IB says the attack on Twilio was part of a wider campaign by the hacking group it’s calling “0ktapus,” a reference to how the hackers predominantly target organizations that use Okta as a single sign-on provider.
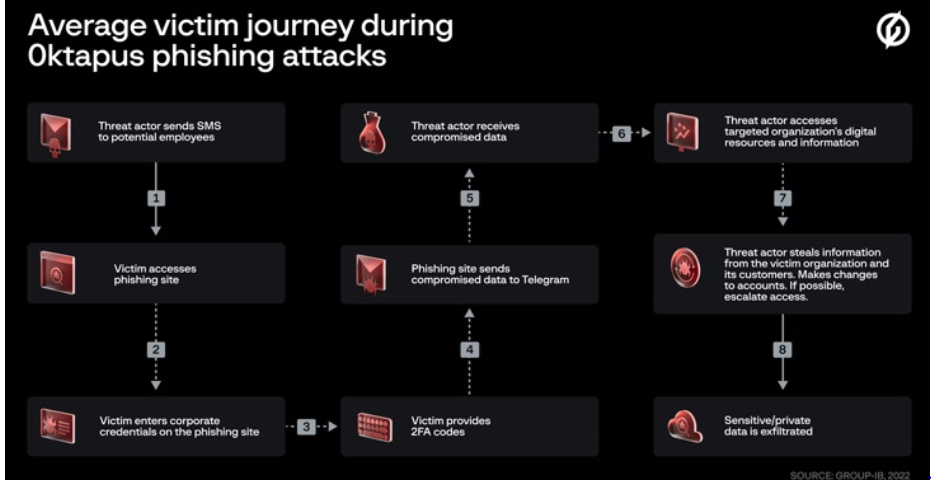
The modus operandi associated sending targets text messages that contains inbound links to phishing internet sites that impersonated the Okta authentication web page of the respective qualified entities.
The exercise has been condemned 0ktapus by Group-IB as a result of the preliminary objective of the assaults was to “get hold of Okta identification credentials and two-factor authentication (2FA) codes from customers of the focused organizations.”
The modus operandi concerned sending targets textual content messages containing hyperlinks to phishing websites that impersonated the Okta authentication web page of the respective focused entities.

A majority of the affected organizations are software companies, followed by those belonging to telecom, business services, finance, education, retail, and logistics sectors.
What’s notable in regards to the assaults is the usage of an actor-controlled Telegram channel to drop the compromised info, which included person credentials, e mail addresses, and multi-factor authentication (MFA) codes.
Group-IB stated it was capable of hyperlink one of many channel directors, who goes by the alias X, to a Twitter and a GitHub account that implies the person could also be primarily based within the U.S. state of North Carolina
“Whereas the risk actor might have been fortunate of their assaults it’s much more seemingly that they fastidiously deliberate their phishing marketing campaign to launch refined provide chain assaults,” Group-IB analyst Roberto Martinez stated.
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!




