
Cyber Security researchers disclosed vulnerability details of multiple popular browsers about an Address Bar Spoofing vulnerability affecting mobile browsers leaving the door open for spear-phishing attacks and delivering malware.
Address Bar Spoofing:
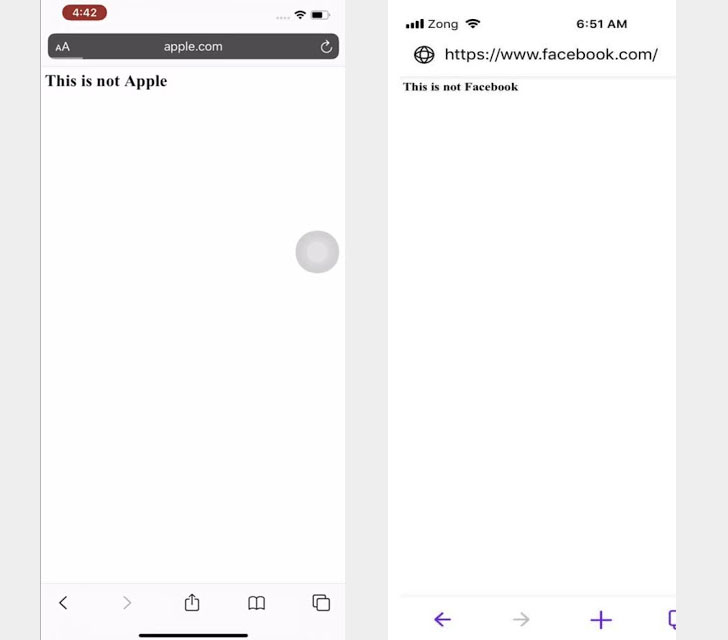
Alteration of a browser’s address bar to display a legitimate address. This is done by running a script that removes the browser’s address bar and replaces it with a fake one, which is made up of text or images.
Cyber Security researchers disclosed vulnerability details of multiple browsers including Apple Safari and Opera Touch, about an address bar spoofing vulnerability.
Other impacted browsers include UCWeb, Yandex Browser, Bolt Browser, and RITS Browser.
Spoofing or masking URLs on desktop web browsers have been an old tactic in hacker text books to dupe users into downloading malware or succumbing to ransomware.
However, with time, desktop browsers have added multiple safeguards including certificate authentication and URL inspections built into address bars. This has not been possible with mobile browsers, primarily due to the constraint of screen space. Utilizing this, hackers are seemingly running malicious scripts on webpages, which would force a website to reload.
During this reload loop that the hackers are routing your webpage to a malicious site. To disguise this bit, the hackers were so far using the address bar vulnerabilities to spoof or mask the URL displayed.
Put differently; an attacker can set up a malicious website and lure the target into opening the link from a spoofed email or text message, thereby leading the recipient into downloading malware or risk getting their credentials stolen.
However, Rapid7 notes that all other browsers contacted by them, including UC Browser, Yandex, Bolt, and RITS, have not even responded to multiple attempts made by the researchers to contact them and report the flaw. With UC and Yandex having a considerable volume of users, this is an alarming issue that must be addressed with urgency.
Until the issues are resolved, users are advised to stick to reliable web browsers such as Google Chrome and Mozilla Firefox and keep an eye out for security bulletins that regularly report such flaws.







