
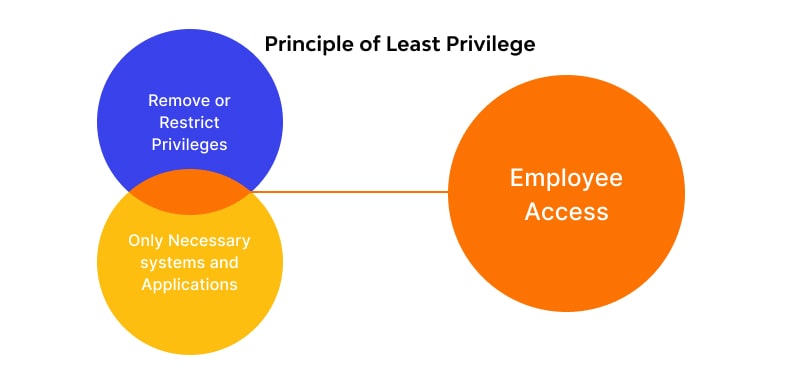
The principle of least privilege (POLP), also named the “principle of least authority” (POLA) or “the principle of minimal privilege” (POMP), stands for a cybersecurity best practice based upon granting the minimum required access that a user needs to perform an assigned task.
When your organization operates by the principle of least privilege, users are granted the bare minimum of privileges to resources such as networks, systems and applications. By establishing least privilege in the context of aZero trust security model, organizations will significantly mitigate the risk of compromise, breach and illicit access to high-value data.
There are 2 major concepts related to POLP:
1. Privilege bracketing
Privilege bracketing refers to the practice of reducing users’ permission levels to the shortest timeframe possible for them to complete a task and afterward de-escalating their rights. Unlike standard user accounts, admin accounts have increased privileges and therefore pose higher risks.
2. Privilege creep
Also called permission bloat, the privilege creep or the access creep is a concept that applies to users who gradually gather unnecessary permissions.
Benefits of the Principle of Least Privilege
- Reduces malware propagation
- Reduced attack surface and enhanced security
- Facilitates audit preparedness
- Safeguards against the human element
Practical Examples of the Principle of Least Privilege
Remote Access
Remote work has increased dramatically since the start of 2020. The shift has brought a host of new challenges as the line between home and work has blurred.
Some organizations attempt to secure access to a network using a VPN. This opens them up to a host of vulnerabilities.With the principle of least privilege, remote access is granted only as needed, limiting the reach and opportunity for an attack to take hold.
Phishing Attacks
Here’s another example. Imagine a new marketing specialist joins your organization and is granted administrator access to his personal laptop as a way to ease friction. If this person clicks on an attachment or link in a phishing email and loads malware onto his system, it could cause far-reaching damage.
Under the principle of least privilege, the impact of the attack would be isolated to a narrow band of resources. On the other hand, if the user has root access or superuser privileges, the infection could spread, potentially modifying account settings and corrupting or accessing sensitive data from across the network.




