
State-backed hackers part of Russia’s Federation Foreign Intelligence Service (SVR) have started using Google Drive legitimate cloud storage service to evade detection.
APT29, also tracked beneath the monikers Cozy Bear, Cloaked Ursa, or The Dukes, has been characterised as an structured cyberespionage team doing the job to gather intelligence that aligns with Russia’s strategic aims.
Some factors of the advanced persistent threat’s actions, such as the notorious SolarWinds offer chain attack of 2020, are individually tracked by Microsoft underneath the name Nobelium, with Mandiant contacting it an evolving, disciplined, and hugely expert risk actor that operates with a heightened amount of operational security.”
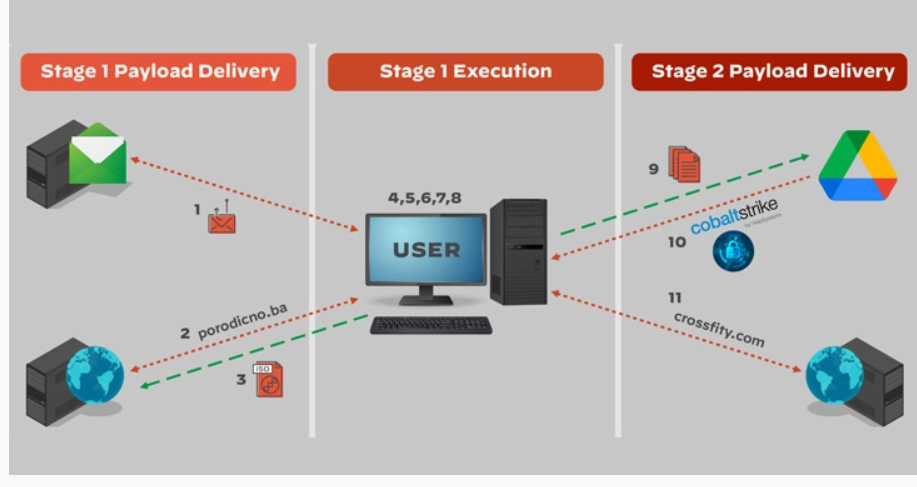
What is improved in the newer iterations is the use of cloud companies like Dropbox and Google Travel to conceal their steps and retrieve added malware into target environments. A second edition of the attack observed in late May well 2022 is explained to have tailored further to host the HTML dropper in Dropbox.
“The use of DropBox and Google Drive services […] is a new tactic for this actor and one that proves challenging to detect due to the ubiquitous nature of these services and the fact that they are trusted by millions of customers worldwide,” the researchers said.
The findings also coincide with a new declaration from the Council of the European Union, calling out the spike in malicious cyber activities perpetrated by Russian threat actors and “condemn[ing] this unacceptable behavior in cyberspace.”
Conclusion
The researchers reiterated that the ubiquity of Google Drive, Dropbox and other popular cloud services, that “are trusted by millions of customers worldwide,” means that “all organizations [should] review their email policies” and the details included in the report to address the threat.
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!




