Hackers are again targeting developers and AI users by creating fake versions of popular tools on GitHub....
Internet Security
Researchers at Guardio Labs have uncovered a large and highly organized phishing operation known as AccountDumpling, which...
A newly identified campaign called EtherRAT is targeting enterprise environments by combining SEO manipulation, GitHub abuse, and...
A newly uncovered Android spyware platform is changing how surveillance malware spreads. Instead of being a single...
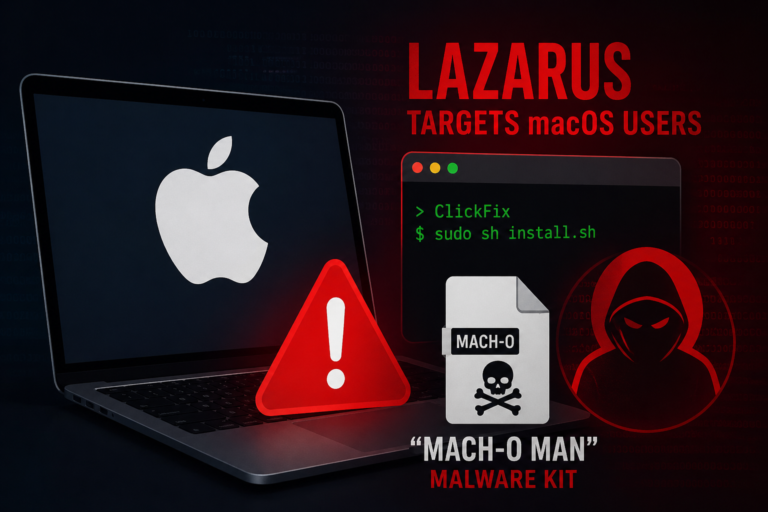
The Lazarus Group is actively using ClickFix-style social engineering to deploy a new macOS malware framework called...