
Attackers are exploiting zero-day in Pulse Secure VPNs to breach organisations — (CVE-2021-22893)
0-Day Vulnerability
Security mitigations released for zero-day vulnerability to assist with determining if systems have been impacted.
Researchers discovered a critical zero-day authentication bypass vulnerability (CVE-2021-22893) that is currently being exploited in the wild and for which there is no patch yet.
FireEye on Tuesday, “A combination of prior vulnerabilities and a previously unknown vulnerability discovered in April 2021, CVE-2021-22893, are responsible for the initial infection vector”
In addition, the severity is marked with base score 10.
Attack Stage
According to FireEye, Attacks staged by UNC2630 are believed to have commenced as early as August 2020, before they expanded in October 2020.
In addition, when UNC2717 began repurposing the same flaws to install custom malware on the networks of government agencies in Europe and the U.S.
Also, the incidents continued until March 2021.
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!
On the other hand, it is identifying 12 malware families associated with the exploitation of Pulse Secure VPN appliances.
One of these (UNC2630) is believed to operate on behalf of the Chinese government and is possibly connected to APT5 (aka Manganese).
Another (UNC2717) could not be definitely tied to a government or known APT group.
However, the list of malware families is as follows –
- UNC2630 – SLOWPULSE, RADIALPULSE, THINBLOOD, ATRIUM, PACEMAKER, SLIGHTPULSE, and PULSECHECK
- UNC2717 – HARDPULSE, QUIETPULSE, AND PULSEJUMP
Two additional malware strains, STEADYPULSE and LOCKPICK, deployed during the intrusions have not been linked to a specific group, citing lack of evidence.
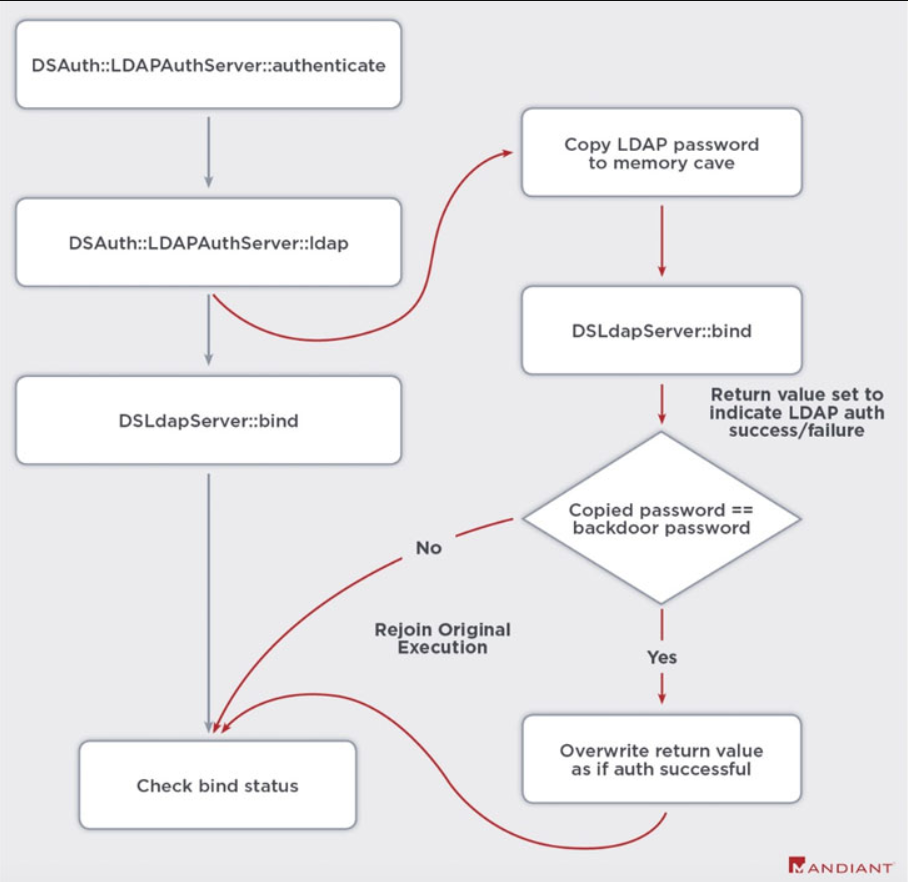
By exploiting multiple Pulse Secure VPN weaknesses
- CVE-2019-11510
- CVE-2020-8260
- CVE-2020-8243
- CVE-2021-22893
UNC2630 have harvested login credentials, using them to move laterally into the affected environments.
However, In order to maintain persistence to the compromised networks the threat actors perform
- firstly, Pulse Secure binaries and scripts to enable arbitrary command execution
- secondly, inject web shells capable of carrying out file operations
- and, running malicious code.
Security Recommendation
Pulse Secure customers are recommended to upgrade to PCS Server version 9.1R.11.4 when it becomes available.
Where a fix for the issue is expected to be in place by early May.
Check for the IOC’s in – https://kb.pulsesecure.net/articles/Pulse_Secure_Article/KB44755








After looking at a few of the blog articles on your web page, I really like your
technique of blogging. I saved as a favorite it to my bookmark site list and will be checking back soon.
Please check out my web site too and tell me what you think.