
A new RAT malware targeting Android devices has been discovered, capable of executing additional commands compared to other RAT malware. It can also conduct phishing attacks by masquerading as legitimate applications such as Snapchat, Instagram, WhatsApp, Twitter, and Google, to harvest credentials from victims.
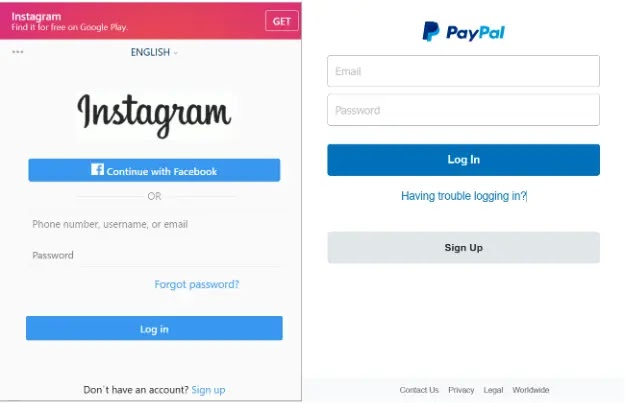
Sonicwall’s deeper investigation revealed multiple HTML files in its assets folder, which replicate login pages of various legitimate applications. These files harvest users’ credentials and transmit them back to the C2 server.
Android Malware Mimics Social Media Apps
The malware’s infection chain begins after the malicious application is installed on the victim’s Android devices. During installation, it requests Accessibility service and Device admin permission to seize control over the installed device and carry out additional malicious actions.
The distribution method of this malware remains unclear, but researchers speculate it will utilize traditional social engineering techniques. Once installed, the malware communicates with the C2 server to receive instructions and commands for specific tasks.
The malware executes the following commands:
The C2 URL is embedded in the resource file.
Upon receiving commands from the C2 server, the malware harvests credentials from browsers and other Android applications by presenting a fake login page using HTML files (phishing).
When victims enter their credentials on these phishing pages, they are collected and shared with the showTt function.
Furthermore, the malware gathers the list of phone numbers stored on the victim’s device and tries to alter the device’s wallpaper when certain conditions are met. If the ‘str’ parameter matches the decrypted value to 0, 1, or 2, the condition for changing the wallpaper is associated with a particular resource.
The malware retrieves information about installed applications from the victim’s device. Upon deeper analysis of the code, it was found that the malware utilizes the CameraManager to toggle the flashlight on/off on the victim’s device. Additionally, it sends a message to a specific number based on inputs received from the C2 server.
Indicators Of Compromise
- 0cc5cf33350853cdd219d56902e5b97eb699c975a40d24e0e211a1015948a13d
- 37074eb92d3cfe4e2c51f1b96a6adf33ed6093e4caa34aa2fa1b9affe288a509
- 3df7c8074b6b1ab35db387b5cb9ea9c6fc2f23667d1a191787aabfbf2fb23173
- 6eb33f00d5e626bfd54889558c6d031c6cac8f180d3b0e39fbfa2c501b65f564
- 9b366eeeffd6c9b726299bc3cf96b2e673572971555719be9b9e4dcaad895162
- a28e99cb8e79d4c2d19ccfda338d43f74bd1daa214f5add54c298b2bcfaac9c3
- d09f2df6dc6f27a9df6e0e0995b91a5189622b1e53992474b2791bbd679f6987
- d8413287ac20dabcf38bc2b5ecd65a37584d8066a364eede77c715ec63b7e0f1
- ecf941c1cc85ee576f0d4ef761135d3e924dec67bc3f0051a43015924c53bfbb
- f10072b712d1eed0f7e2290b47d39212918f3e1fd4deef00bf42ea3fe9809c41




