
Ransomware red button on keyboard, 3D rendering
A new analysis of tools put to use by the Black Basta ransomware operation has identified ties between the threat actor and the FIN7 (aka Carbanak) group.
Black Basta has been active since April 2022, like other ransomware operations, it implements a double-extortion attack model.
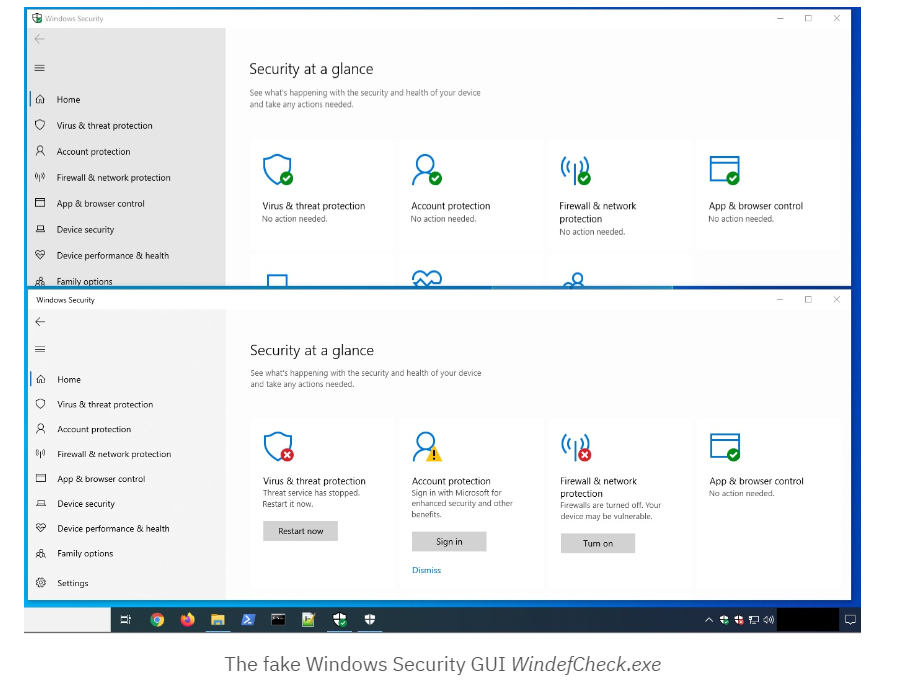
Black Basta was observed deploying a custom EDR evasion tool used to displays a fake Windows Security GUI and tray icon which leaves users with the fake impression that Windows Defender is working properly, while in fact it has been disabled, along with EDR and antivirus tools.
The Sentinel Labs’s analysis revealed that Black Basta ransomware operators develop and maintain their own toolkit, they documented only collaboration with a limited and trusted set of affiliates.
The threat actors were disabling Windows Defender executing the following scripts:
\Windows\ILUg69ql1.bat \Windows\ILUg69ql2.bat \Windows\ILUg69ql3.bat
The attackers also used the same naming convention (ILUg69ql followed by a digit) for batch scripts found in different intrusions.
powershell -ExecutionPolicy Bypass -command “New-ItemProperty -Path ‘HKLM:\SOFTWARE\Policies\Microsoft\Windows Defender’ -Name DisableAntiSpyware -Value 1 -PropertyType DWORD -Force” powershell -ExecutionPolicy Bypass -command “Set-MpPreference -DisableRealtimeMonitoring 1” powershell -ExecutionPolicy Bypass Uninstall-WindowsFeature -Name Windows-Defende
One sample was packed with a backdoor — called BIRDDOG — that has been used in multiple past FIN7 operations and that beacons to a command-and-control server using the same bulletproof hosting services that FIN7 deploys. Code samples found on public malware repositories using the same packer pre-dated the creation of BIRDDOG by two months and revealed a Cobalt Strike DNS beacon. After further analysis, the researchers concluded that the packer used to compress BIRDDOG is an updated version.
“At this point, it’s likely that FIN7 or an affiliate began writing tools from scratch in order to disassociate their new operations from the old,” researchers Antonio Cocomazzi and Antonio Pirozzi said. “It is likely that the developer(s) behind their tools to impair victim defenses is, or was, a developer for FIN7.”
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!




