
Microsoft says that some of the Exchange Server flaws addressed as part of the August 2022 Patch Tuesday also require admins to manually enable Extended Protection on affected servers to fully block attacks.
The company patched 121 flaws today, including the DogWalk Windows zero-day exploited in the wild and several Exchange vulnerabilities ( CVE-2022-21980 , CVE-2022-24477 , and CVE-2022-24516 ) rated as critical severity and allowing for privilege escalation.
Remote attackers can exploit these Exchange bugs to escalate privileges in low-complexity attacks after tricking targets into visiting a malicious server using phishing emails or chat messages.
Extended Protection
However, Microsoft says that admins also need to enable Extended Protection (EP) after applying today’s security updates to make sure that threat actors won’t be able to breach vulnerable servers.
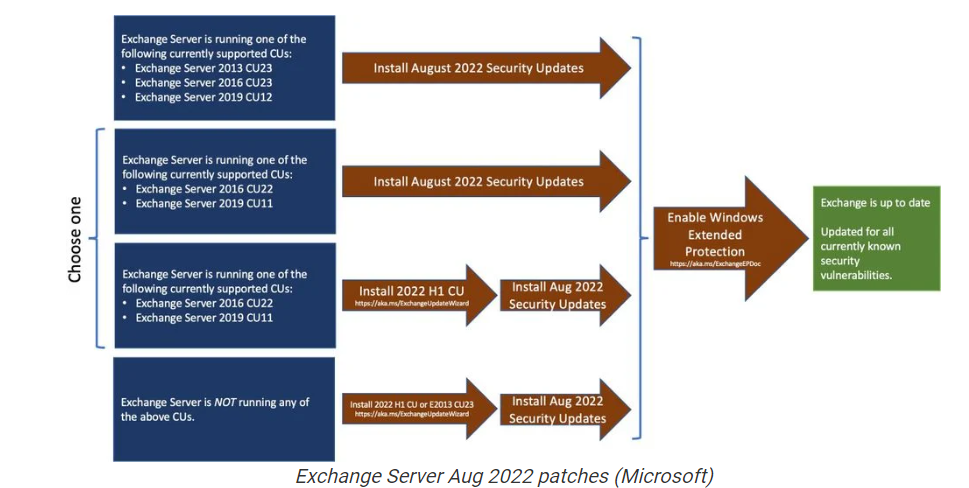
A script provided by Microsoft is available to enable this feature, but admins are advised to “carefully” evaluate their environments and review the issues mentioned in the script documentation before toggling it on their Exchange servers.
“Microsoft analysis has shown that exploit code could be created in such a way that an attacker could consistently exploit this vulnerability. Moreover, Microsoft is aware of past instances of this type of vulnerability being exploited,” the company says.
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!




