
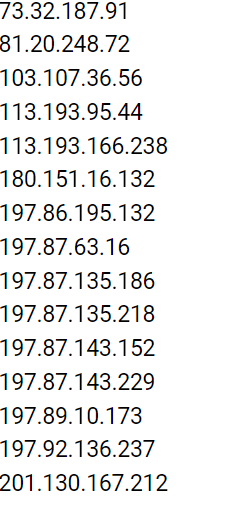
As of late June 2023, the QakBot (aka QBot) malware operators have established 15 new command-and-control (C2) servers.
The findings come as a follow-up to Team Cymru’s previous malware infrastructure analysis, emerging just over two months after Lumen Black Lotus Labs disclosed that 25% of its C2 servers remain active for only a single day.
QakBot Malware
QakBot, also known as QBot, is a sophisticated banking Trojan malware that targets financial institutions and their customers. It steals sensitive information, creates botnets, and establishes a command-and-control network to control infected computers remotely.
The cybersecurity firm reported that QakBot has a consistent pattern of going on an extended break each summer and then resurfacing sometime in September. This year, its spamming activities halted around 22 June 2023.
QakBot’s C2 network has a tiered architecture similar to Emotet and IcedID. The C2 nodes communicate with Tier 2 (T2) C2 nodes hosted on VPS providers in Russia.
Most of the bot C2 servers, which communicate with victim hosts, are in India and the U.S. The outbound T2 connections lead to IP addresses primarily based in the U.S., India, Mexico, and Venezuela.
Additionally, there is a BackConnect (BC) server alongside the C2s and Tier 2 C2s, which turns the infected bots into proxies for other malicious activities.
Team Cymru’s latest research shows a significant decrease in the number of C2s communicating with the T2 layer, leaving only eight remaining. This reduction was partly due to Black Lotus Labs’ null-routing of the higher-tier infrastructure in May 2023.
An analysis of NetFlow data reveals a pattern where increased outbound T2 connections often follow spikes in inbound bot C2 connections. Conversely, spikes in outbound T2 connections coincide with a decline in bot C2 activity.
Team Cymru explained that QakBot’s strategy of using victims as C2 infrastructure with T2 communication results in double harm to users – first in the initial compromise and then in the risk of being publicly identified as malicious.
Indicators of Compromise
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!




