
Security researchers have recently discovered ThirdEye, an information stealer designed for Windows operating systems. This stealthy malware is capable of collecting sensitive data from computers that have been infected.
ThirdEye Windows-Based Malware
The malware, discovered by Fortinet FortiGuard Labs, was found within an executable file cleverly disguised as a PDF file named “CMK Правила правилания больничных листов.pdf.exe.” This Russian-named file translates to “CMK Rules for issuing sick leaves .pdf.exe.”
The evolving stealer, like other malware families of its kind, is equipped to gather system metadata, including BIOS release date and vendor, total/free disk space on the C drive, currently running processes, register usernames, and volume information. The amassed details are then transmitted to a command-and-control (C2) server.
A notable trait of the malware is that it uses the string “3rd_eye” to beacon its presence to the C2 server.
Currently, there is no substantiated evidence to confirm the active utilization of ThirdEye in real-world scenarios. However, the bulk of the stealer artifacts were uploaded to VirusTotal from Russia, suggesting that the malicious activity primarily targets organizations within Russian-speaking regions.
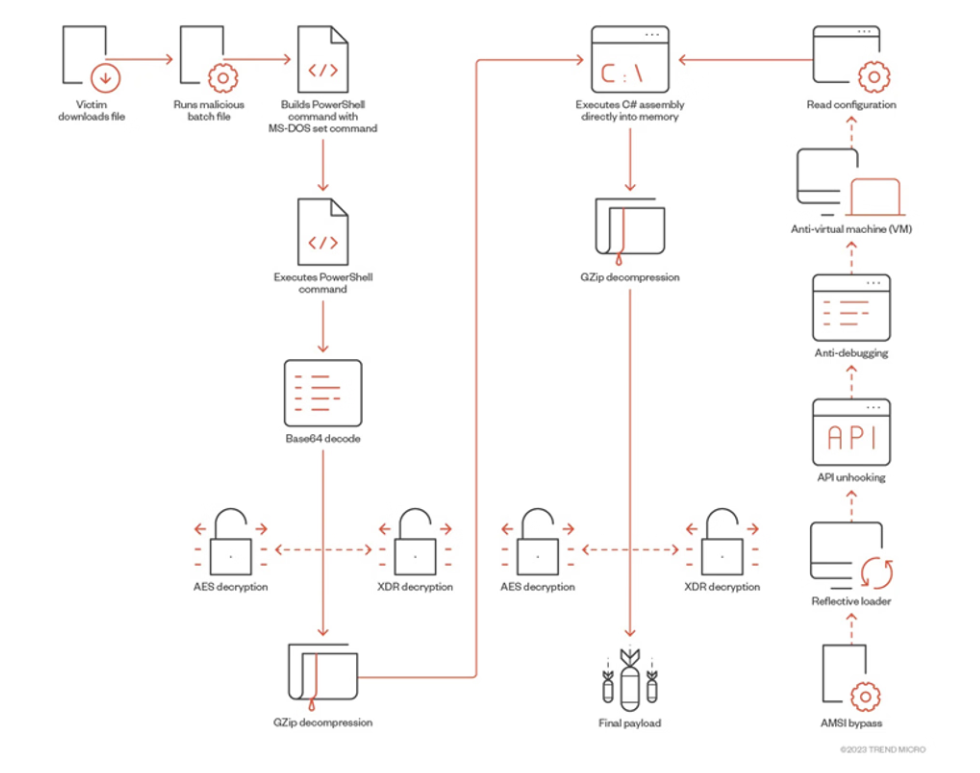
In addition to other targets, video game users have been subject to Python-based ransomware and a remote access trojan known as SeroXen. Notably, SeroXen leverages ScrubCrypt, a commercial batch file obfuscation engine (also known as BatCloak), to effectively evade detection.
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!




