
According to Microsoft, a phishing campaign active since December expanded with new feature, also now bypass Email Gateway.
Phishing Attack
Phishing — a type of social engineering attack often used to steal user data, including login credentials and credit card numbers.
According to Microsoft Defender for Office 365 data shows that this phishing operation is still active today and continues to expand.
More recent campaigns have also used emails that spoof security solutions and productivity tools.
The WMC Global Threat Intelligence Team first detected the threat actors called “Compact” campaigns operating since early 2020.

However, according to WMC Global the threat actors collected over 40K credentials from OWA and O365.
Microsoft’s security experts said, Phishers continue to find success in using compromised accounts on email marketing services to send malicious emails from legitimate IP ranges and domains.
Also, They take advantage of configuration settings that ensure delivery of emails even when the email solution detects phishing.
Trusted Service Notifications
Now, Appspot also abused by phishing campaign to bypass its Email gateway
Where, the threat actors feign legitimacy by sending invites as from video conferencing services, various security solutions, and productivity tools.
On the other hand, taking advantage of compromised accounts/domains — SendGrid and MailGun mail delivery services, phishers send Email to organizations by allowing them as trusted domains.
Which as part of phishing attacks allows threat actors to bypass Secure Email Gateways (SEGs) — luring them to:
- open an attached document embedded with macros
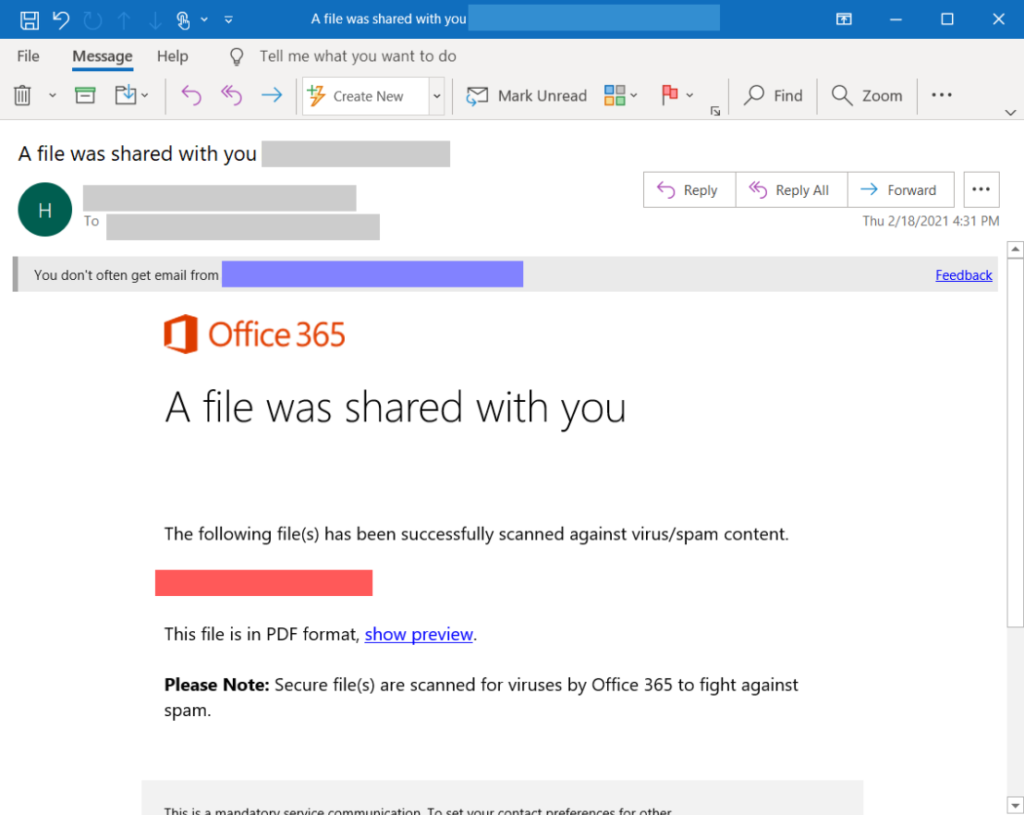
- or, clicking hyperlinks that redirects to malicious phishing pages that mimic like Microsoft Login pages

Importantly, The phishing operation continues to expand as it now also abuses Amazon Simple Email Service (SES) and the Appspot cloud computing platform.
In addition, Appspot confirmed the malicious nature of the reported URLs as shared by Microsoft and used the shared intelligence to find and suspend additional offending projects on Appspot.
However, Microsoft continue working with Appspot as they continue to track this active phishing operation.
Finally, Microsoft advised organizations to review mail flow rules for broad exceptions that may be letting phishing emails through.
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!







Good write-up, I am normal visitor of one’s web site, maintain up the nice operate, and It is going to be a regular visitor for a lengthy time.