
A new IoT botnet malware dubbed RapperBot has been noticed promptly evolving its capabilities because it was 1st discovered in mid-June 2022.
RapperBot Malware
RapperBot has limited DDoS capabilities, it was designed to target ARM, MIPS, SPARC, and x86 architectures.
The malware is a Mirai variant with a few notable, novel features, including ditching the typical Telnet server brute-force approach in favor of attacking SSH servers instead.
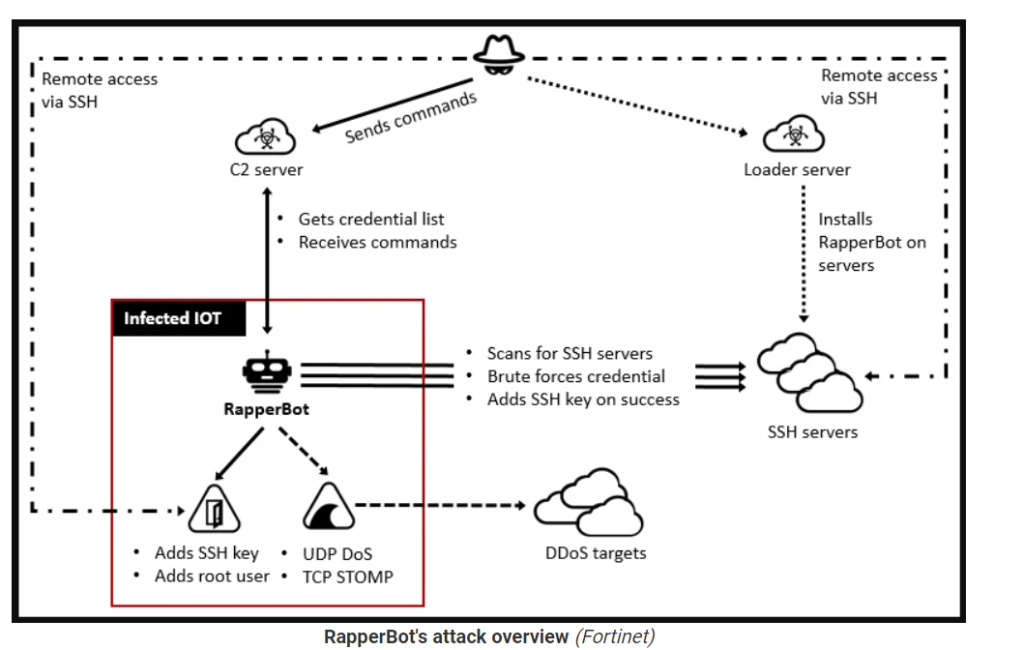
The deviation from traditional Mirai behavior is further shown in its attempt to establish persistence on the compromised host, effectively allowing the hacker to maintain long-term access long after the malware has been removed or the device has been rebooted.
The attacks entail brute-forcing possible targets employing a listing of qualifications gained from a remote server. Upon correctly breaking into a susceptible SSH server, the valid credentials are exfiltrated again to the command-and-command.
The entry is achieved by adding the operators’ SSH general public critical to a particular file known as “~/.ssh/authorized_keys,” allowing the adversary to hook up and authenticate to the server using the corresponding personal private critical with out possessing to furnish a password.
“This offers a threat to compromised SSH servers as menace actors can obtain them even right after SSH credentials have been changed or SSH password authentication is disabled,” the scientists spelled out.
Conclusion about RapperBot Malware
To fend off these kinds of infections, it really is recommended that end users established powerful passwords for devices or disable password authentication for SSH the place feasible.
Experts pointed out that the goal of RapperBot is still unclear.
IOCs from fortinet
Files
92ae77e9dd22e7680123bb230ce43ef602998e6a1c6756d9e2ce5822a09b37b4
a31f4caa0be9e588056c92fd69c8ac970ebc7e85a68615b1d9407a954d4df45d
e8d06ac196c7852ff71c150b2081150be9996ff670550717127db8ab855175a8
23a415d0ec6d3131f1d537836d3c0449097e98167b18fbdbf2efca789748818a
c83f318339e9c4072010b625d876558d14eaa0028339db9edf12bbcafe6828bb
05c78eaf32af9647f178dff981e6e4e43b1579d95ccd4f1c2f1436dbfa0727ad
88bbb772b8731296822646735aacbfb53014fbb7f90227b44523d7577e0a7ce6
Follow Us on: Twitter, Instagram, Facebook to get the latest security news!




